A10 Defend DDoS Protection
A holistic DDoS protection solution that is scalable, precise, and intelligent to ensure optimal user and subscriber experiences
Key Benefits
Used by leading service providers and online gaming platforms, A10 DDoS protection delivers intelligent detection and automated mitigation to maintain uptime against advanced DDoS attacks.
How It Works
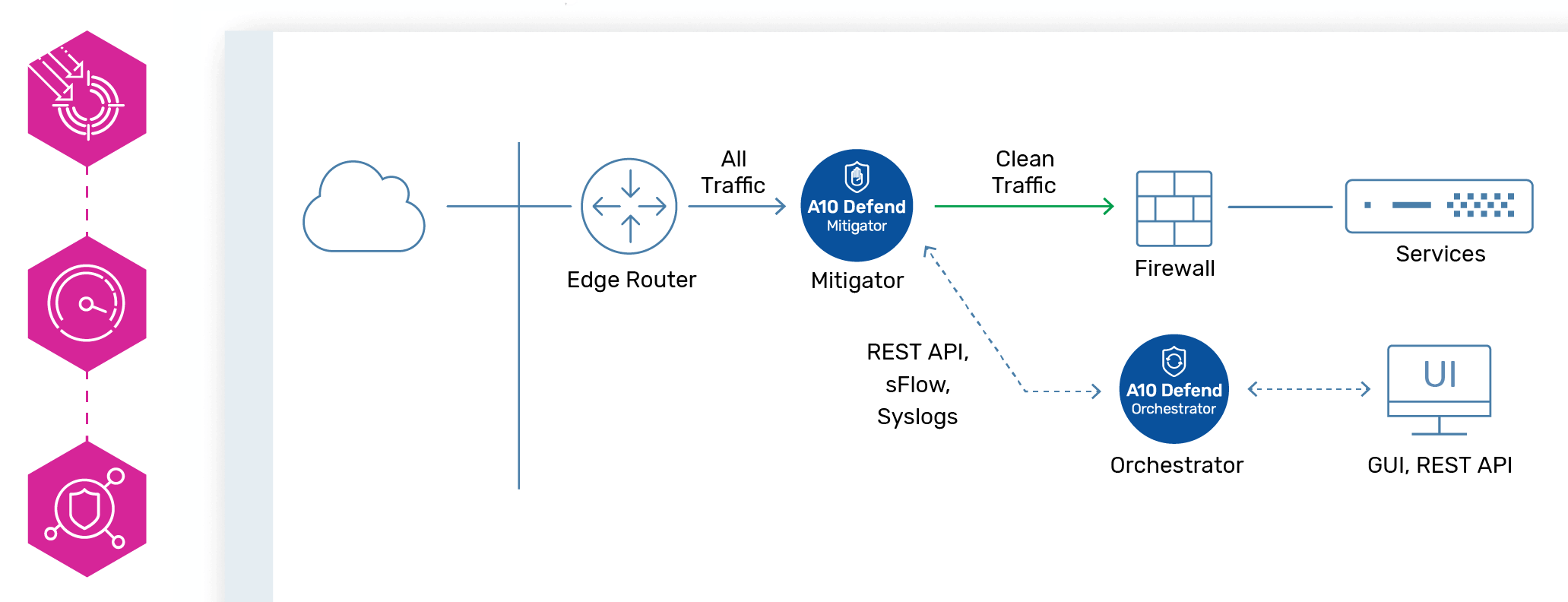
Intelligent DDoS Attack Mitigation
Defend and automatically mitigate multi-vector DDoS attacks with precision and agility.
High-performance protection against DDoS threats ensures network security, with capabilities ranging from 1Gbps to over 1Tbps for comprehensive defense.
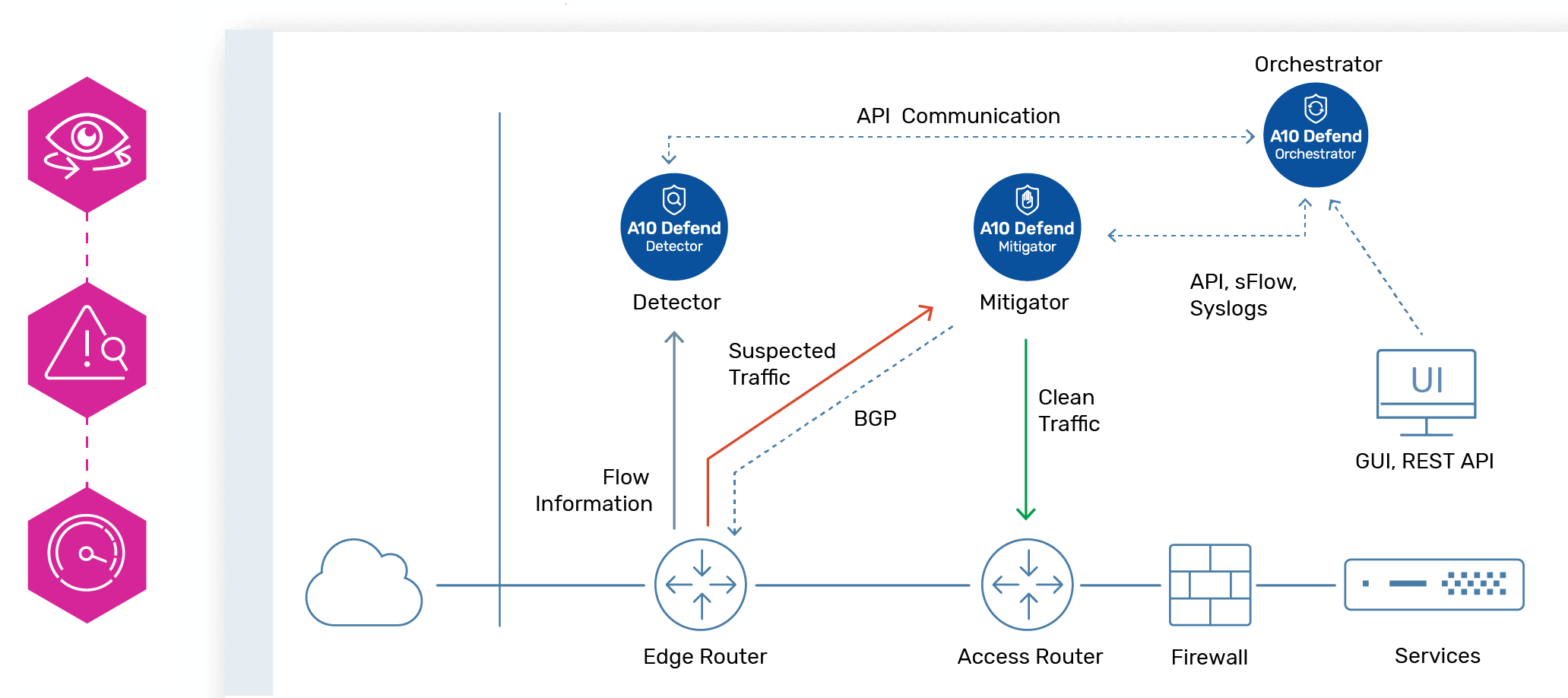
Network-wide Anomaly Detection
Proactive threat visibility and faster DDoS detection with automated traffic behavior profiling.
Continuous analysis of traffic patterns detects anomalies in real time, enabling swift responses to potential threats and maintaining application resilience.
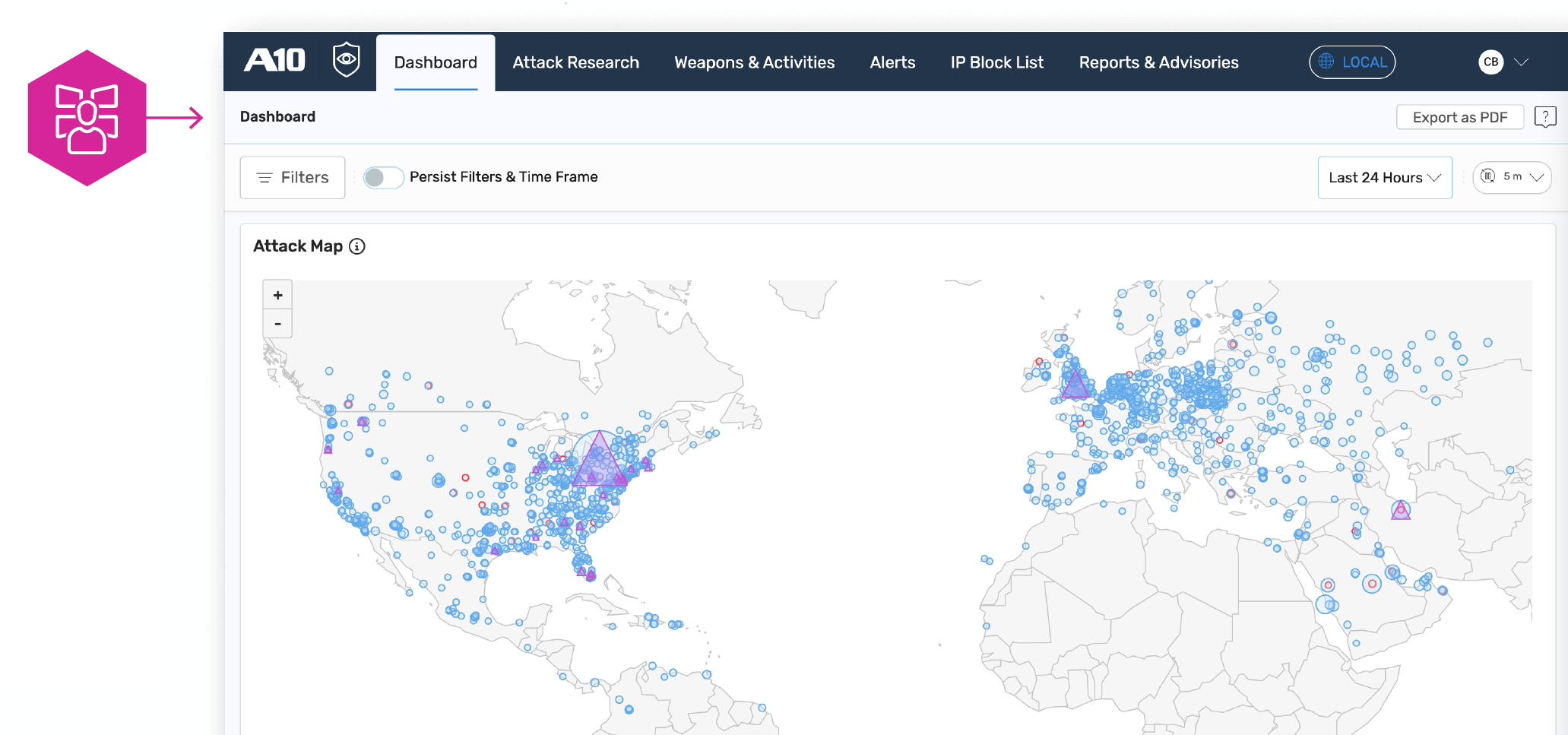
Real-time DDoS Defense Management
Recognize attackers from valid users and block unwanted traffic.
With A10 Control, enable organizations to gain a holistic view of their defenses, allowing for rapid identification and remediation of DDoS attacks while ensuring that security policies are consistently enforced across the network.
Proactive Threat Protection
AI-driven intelligence and research delivered as a service.
A standalone SaaS platform establishes a robust layer of defense by offering actionable insights, automated threat detection, and customizable blocklists, enhancing the overall security posture against evolving threats.
Key Features
Zero-day Automated Protection
Expert systems evaluate blocking filters in real-time, ensuring optimal protection with fast, automated responses and no manual intervention.
Precision
Adaptive policy engine minimizes damage using machine learning for zero-day attack responses and accurate threat validation.
Industry-leading Performance
Unmatched performance density up to 220 Gbps per RU with high-speed processing of 440 Mpps, managing 6M flows simultaneously—twice the industry benchmark.
Advanced DDoS Detection
Fast, automated detection at scale with minimal configuration. Intelligent filtering by IP and real-time threat assessment.
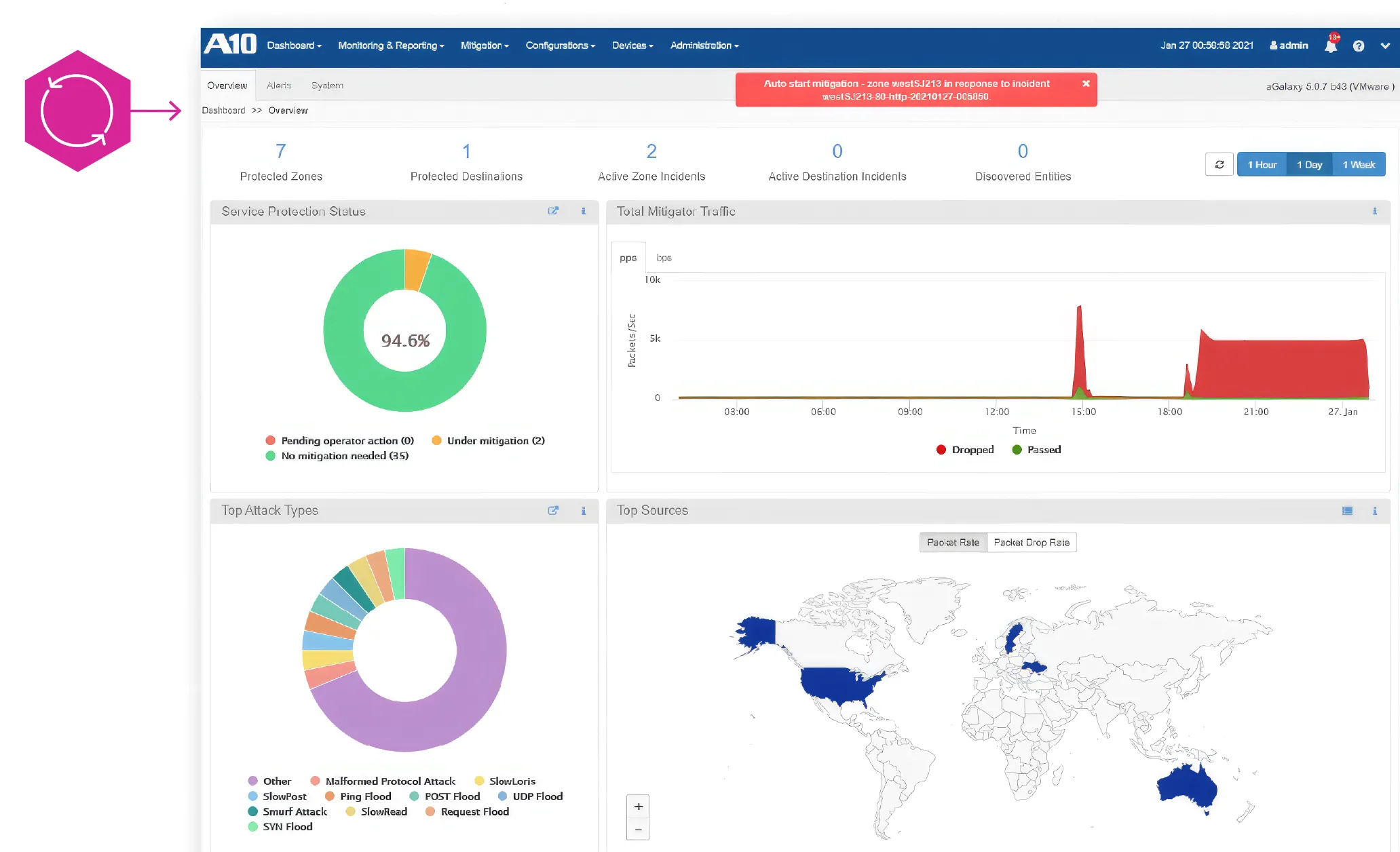
Management and Analytics
Real-time dashboard for device management. Get insights with live visualization and geolocation tracking to enhance security.
DDoS-specific Intelligence
Customizable blocklists automatically updated. Teams receive intelligence on attack vectors and can block threats proactively as often as every 15 min.
Threat Intelligence
Over three dozen security threat intelligence sources to instantly recognize and block malicious traffic
What Our Customers Are Saying
A10 Networks Enhances Application Speed and Uptime With Advanced Delivery Features
“My overall experience with A10 Networks has been very positive. The platform delivers exceptional performance, especially with its advanced load balancing and application delivery capabilities. We have seen significant improvements in application speed and uptime after deploying A10’s and ADC solution.”
Great tool with multi-layered defense to reliably mitigate threats such as SQL injection
“It is a robust DDoS tool with comprehensive anti-malware, intrusion prevention and firewall features that allows us to create policies and take control over the block and filters to monitor and frequently analyze the incoming network traffic.”
Seeing is believing. Schedule a live demo today.
Request a DemoSecurity Research Report
DDoS Attacks – Evolving Game of Threat Actors
This report summarizes data collected by the A10 security research team and provides a snapshot of a constantly changing global weapons landscape with insight into the sources, types and other characteristics of DDoS weapons.
Get the Free Report