Twitch Hack, Data Exfiltration Shows Twitch Creator Payouts

It’s not an “if,” it’s a “when.” No matter what you do, no matter how robust your think your cyber defenses are, one way or another your organization will eventually get hacked. If you’re lucky, the consequences of the attack will be minimal—maybe just an easily analyzed and resolved website defacement. On the other hand, should you be unlucky, you might end up like the computer game streaming service, Twitch.
Twitch, acquired by Amazon in 2014 in a $970 million all-cash deal, is the 800-pound gorilla of video game streaming. It also offers esports and music broadcasts. In February 2020, the service delivered content from three million twitch creators every month, served 15 million daily active users, and serviced an average of 1.4 million concurrent users.
The Twitch Hack
When the Twitch game streaming service was hacked on October 6, 2021, the big news story was less about the fact the service got hacked but rather more about the breadth and depth of the data exfiltration: The hackers took a copy of everything on Twitch’s servers including:
- Records of three years of twitch creator payouts
- The entirety of the platform’s source code, “with commit history going back to its early beginnings”
- Mobile, desktop, and video game console source code of Twitch clients
- Source code related to proprietary SDKs and internal AWS services used by Twitch
- An unreleased Steam competitor from Amazon Game Studios
- Data on other Twitch properties including Vapor, IGDB, and CurseForge
- Twitch’s internal security tools
The stolen content was published by an anonymous 4chan user in a 125GB torrent with the message, “Jeff Bezos paid $970 million for this, we’re giving it away FOR FREE.” The user also claimed that this was “part one,” which implies there may be more stolen content to come from the data exfiltration.
One of the biggest problems for Twitch will be the publishing of the game streaming service’s source code because, as with the breach it experienced in 2014, the company will probably have to do a complete system rewrite to reduce the potential attack surface.
While user account login credentials and other personally identifiable information were not revealed, the data leak did include Twitch creator account earnings for the period from August 2019 to October 2021, which had not been previously public.
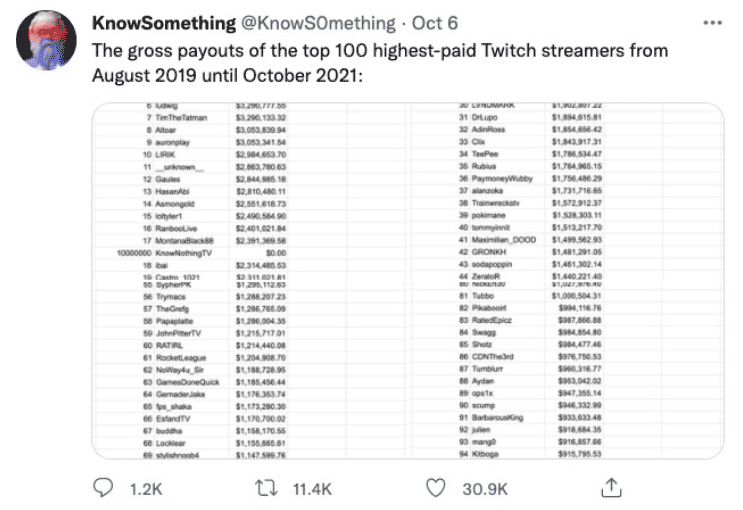
Source: Twitter
How Did the Twitch Hack Happen?
So far, the company hasn’t said much about the cause of the latest Twitch hack other than to say:
“ …the incident was a result of a server configuration change that allowed improper access by an unauthorized third party … Twitch passwords have not been exposed. We are also confident that systems that store Twitch login credentials, which are hashed with bcrypt, were not accessed, nor were full credit card numbers or ACH / bank information.”
As noted, this latest hack was not the first Twitch experienced. In the 2014 breach, which occurred just after the company’s acquisition by Amazon, an engineer discovered traces of unauthorized access in the game streaming service system logs. The incursion was judged as having “the characteristic of a minimally skilled adversary.” In other words, it appeared that an amateur had gained access.
Shockingly, at the time, Twitch had few staff with responsibility for cybersecurity. As a result, the entire company went into mitigation mode with nearly all staff working for two solid months to assess the damage. According to a former employee:
“The hackers had such wide access before they were detected, we basically had to rebuild everything from scratch.”
Another ex-employee commented:
“This [2014] incident was a very worst-case-scenario attack that was entirely preventable. But leadership’s desire to avoid considering the security problem was the root cause… And this more recent incident demonstrates that they didn’t learn anything from the incident in 2014.”
What Could Twitch Have Done?
While the full details of the latest Twitch hack are unclear, given the apparently unlimited access the intruders gained to what is an enterprise-scale system, it’s obvious that there were large systemic weaknesses in the company’s security to permit such a massive data exfiltration.
Preventing such an attack should be of critical importance to any organization with an enterprise-scale network. And the answer is to deploy what is considered to be the current best network security practice: a Zero Trust architecture.
The Zero Trust Model
The National Institute of Standards and Technology defines the Zero Trust model as “a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least-privilege-per-request access decisions in information systems and services in the face of a network viewed as compromised.”
The Zero Trust model has seven main principles:
- All data sources and computing services are considered resources.
- All communication is secured regardless of network location.
- Access to individual enterprise resources is granted on a per-session basis.
- Access to resources is determined by dynamic policy—including the observable state of client identity, application/service, and the requesting asset—and may include other behavioral and environmental attributes.
- The enterprise monitors and measures the integrity and security posture of all owned and associated assets.
- All resource authentication and authorization are dynamic and strictly enforced before access is allowed.
- The enterprise collects as much information as possible about the current state of assets, network infrastructure and communications and uses it to improve its security posture.
It’s the last principle that makes the Zero Trust model effective in the real world because real-time monitoring of resources ensures that unauthorized access is detected as it happens. But achieving this requires in-depth and comprehensive monitoring of all network communications, which according to the second Zero Trust model principle must be secured.
The solution to this “deep” monitoring requirement is TLS and SSL inspection (also called “break and inspect”) which involves decrypting secured communications at the network edge as well as within network segments and looking not only for unauthorized access but also for signs of data exfiltration by watching for key business content patterns (e.g., social security numbers, file types, unexpectedly large data transfers, etc.).
Related Resources
- Zero Trust is Incomplete Without TLS Decryption (White Papers)
- Zero Trust and the New Normal for Cybersecurity (Webinar)
- TLS, Compliance and Zero Trust – Protecting Users from Cyberattacks (Webinar)
How A10 Can Help
If your organization has not adopted a Zero Trust architecture combined with deep TLS and SSL inspection, now is the time to start rethinking your security position because the threat environment is more invasive and dangerous than ever.
A10 Networks Thunder® SSL Insight delivers full traffic visibility through centralized TLS and SSL inspection and its “decrypt once, inspect many times” approach allows you to inspect all traffic in real time, while avoiding performance penalties and simplifying monitoring operations.