Yikes! Another DDoS Weapon, WS-Discovery Amplification Attacks
Web Services Dynamic Discovery Services Weaponized for DDoS
Reflected amplification attacks continue to be the DDoS attacker’s weapon of choice. From an attacker’s perspective, that makes sense because there is no malware to develop or intrusion involved in exploiting someone else’s computing and networking capabilities. Simply, spoof your victim’s IP address as the requester and a server with a reflected amplification provisioned service, e.g., DNS resolver or NTP server, and it will happily provide an amplified response directed toward the victim or to anyone else who asks. Repeat this to a hundred, a thousand, tens of thousands, or even a million of these exposed servers, and you have a DDoS attack that will catch your customer’s attention.
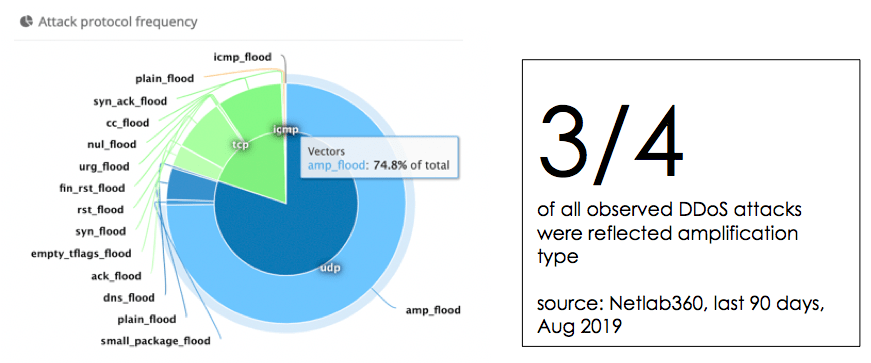
WS-Discovery, the New DDoS Weapon
But exploiting these servers in amplified attacks isn’t new news. What is new to DDoS defenders and the rest of us internet users, is that attackers have found yet another amplification tool. That new weapon is the Web Service Dynamic Discovery protocol (WS-Discovery or WSD) as recently highlighted by Catalin Cimpanu in ZDNet.
WS-Discovery is a multicast, UDP-based communications protocol for finding “who is near me.” WSD works similar to how UPnP makes finding and connecting to things in your home easier. One common IoT-based WSD business use case is IP cameras and DVRs discovering each other.
The problem comes when people and IT departments make these devices accessible to the internet. WSD should be a LAN technology, not running rampant over the internet. And that is what DDoS attackers and DDoS-for-hire services (booters) have started to exploit.
Here are a few of the ugly numbers that A10 Networks’ threat intelligence researchers found:
- >800k sources that respond to WS-Directory requests
- Observed amplification factor up to 95x
- Vietnam, Brazil, United States, Republic of Korea, and China host 72 percent of the discovered inventory
Now here’s the problematic part. The thing is, WS-Discovery-based attacks are not so easy to identify and deflect. It has a nasty characteristic of using random UDP high ports for communicating their amplified response back to the victim. To better explain the implication of this usage of UDP high ports, we need to go back to UDP port usage convention.
UDP port assignment convention
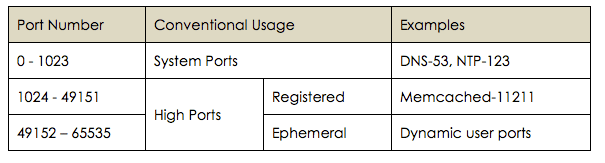
Most protocols follow an established convention of using predefined ports assigned by IANA for communicating their responses. For example, the record-breaking 1.3Tbps Github attack in 2018 leveraged ~50K exposed Memcached servers (side note: why do people expose back-end object caching servers to the internet? Nuts). Memcached servers communicate their responses back over source port 11211. That makes it relatively easy to identify. If you see a huge amount of traffic, all with source port 11211, a port that should never have any traffic coming from the internet, your next action should be pretty clear. Write a router rule or make a BGP Flowspec announcement to block UDP source port 11211 upstream.
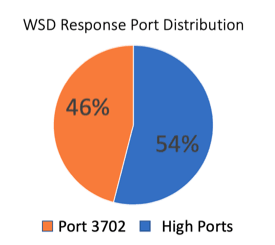
However, with WS-Discovery, A10 Networks researchers have found that many WSD implementations respond using source port 3702, as expected, but nearly half will respond over UDP high ports. Yikes! A flood of UDP packets with random high ports and unique data payloads per host make network-level defenses complicated. Commonly used techniques like BGP Flowspec port blocking aren’t going to work by themselves.
But all is not lost. A10 Networks’ threat researchers, led by Rich Groves and Manoj Senguttuvan, have put together a detailed advisory on this new attack strategy. The threat advisory explains the attack characteristics, the geo-location of the vulnerable servers, which ASN hosts their networks and PCAPs of the amplified responses. More importantly, the advisory describes defensive techniques that work, as well as commonly used techniques that just won’t.
Mitigation Strategies Discussed
- Layer 3/4 filters
- Impact of blocking fragments
- Blacklisting with DDoS weapons intelligence
- Zero-day Attack Pattern Recognition (ZAPR)
You can read the details of this threat report here: WS-Discovery Amplification Attack
To learn more about A10 Networks’ DDoS defense and how to take advantage of actionable DDoS weapons Intelligence, follow these links: