Mayors of America, Beware! – Ransomware is coming to town

Ransomware attacks have been around for a long time. We saw a huge spike in ransomware attacks, and the resulting damages, from 2016 to 2017, including the devastating WannaCry attack of 2017 that cost organizations as much as $4 billion in damages. There was a slight lull in ransomware activities in the 2018 but in 2019 ransomware is back with a quarter-over-quarter increase of around 195 percent at the start of the year.
There is also a new, disturbing trend on the rise: American cities are specifically being targeted with ransomware attacks and the numbers, as well as the damages incurred, are dramatically increasing.
Let’s dig deeper into this trend and look at some of the most recent attacks, what this means in terms of damages, how these attacks can leverage encryption to bypass our defenses, and how we can avoid falling victim to such attacks.
American Cities are the New Target
Several American cities have been targeted with ransomware attacks in recent days. These attacks have been devastating to the government offices involved and to the citizens at large.
Unfortunately, there’s no getting away from ransomware attacks. Cities are faced with a dilemma: pay the large ransom amounts and create a dangerous precedent for future attackers, OR don’t pay the ransom, lose all the data, and rebuild your infrastructure from scratch. Either way, the cities and their inhabitants lose.
Let us look at some of the most recent and major ransomware attacks on our cities, analyze the costs, effects, and the different ways they were dealt with.
Baltimore, Maryland
In early May, Baltimore government offices were hit by a ransomware attack. The infamous “RobbinHood” attack encrypted critical files on the government’s systems and a demand for 13 bitcoins was made (over $100,000). Even though the officials immediately notified the FBI and took their systems offline, the damage had already been done. The city’s voicemail, email, parking fines database, and systems for payments of water bills, property taxes and vehicle citations went down, delaying, among other things, over 1,500 home sales in the city.
Baltimore refused to pay the ransom and ended up having to rebuild their entire infrastructure from scratch. The process has been slow, and the city has been struggling to get back on its feet. The overall cost of the attack has been estimated at around $18 million due to missed or delayed payments.
Riviera Beach, Florida
The city of Riviera Beach in Florida was hit with a ransomware attack towards the end of May 2019, while the attack in Baltimore was still going on and wreaking havoc. The attack was unleashed when an employee of the police department opened an email, infecting computers across the city’s network and paralyzing the city’s operations.
The city ended up holding a vote and paying the hefty ransom of 65 bitcoins ($600,000). This, on top of the almost $1 million spent on upgrading their dated computer systems in multiple government offices, has set the city back by quite a margin, even though some of the upgrades and damages are covered by insurance.
Lake City, Florida
Less than a week after Riviera Beach was attacked, Lake City was hit with a catastrophic ransomware attack. The small city of just 65,000 inhabitants was met with a ransom demand of almost $500,000, or 42 bitcoins. The attack was carried out in a similar fashion to the one in Riviera Beach. It is believed that a city employee downloaded an infected file, setting off a chain of events that crippled the city’s cyber infrastructure. The attack comprised of a combination of three separate attacks, starting with the Emotet trojan, that downloaded the TrickBot trojan after installing itself, and the Ryuk ransomware, which eventually encrypted critical files on the city’s systems.
The city ended up holding a vote and paying the ransom of $480,000, in order to recover the files encrypted by the attack. After paying the ransom, the city also fired its director of information technology.
…And More
The attacks explored above are just the most recent ones that stand out. Apart from those, there have been others in this new wave of ransomware attacks on American cities.
These attacks are becoming increasingly dangerous and widespread:
- Atlanta, Georgia – March 2018
- Imperial County, California – April 2019
- Greenville, North Carolina – April 2019
- Cleveland, Ohio – April 2019
- Augusta, Maine – April 2019
- Albany, New York – April 2019
- Lynn, Massachusetts – May 2019
- Cartersville, Georgia – May 2019
- The village of Key Biscayne, Florida – June 2019
What is Ransomware?
Ransomware is not a new thing; in fact, the first ransomware attack was carried out in 1989. However, within the last few years there has been an increase in the number and scale of these type of attacks where your data is held for ransom.
Ransomware is a form of malware that infects a target computer, encrypts some or all the data on it, and presents the victim with a “ransom note” explaining how they can pay to get their data back. The payment is almost always requested to be made in bitcoins due to simple fact that payments cannot be tracked.
Most of the time, ransomware attacks are carried out using phishing, spear phishing or other social engineering attacks, where the victim is tricked into either clicking a link in an email or downloading an attachment.
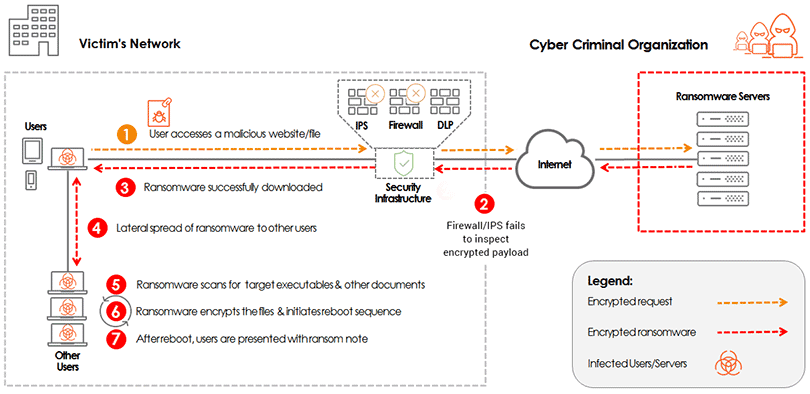
The use of encryption, as a cover to bypass your security stack, is not uncommon as it lets the attackers slip through your defenses undetected, planting trojans and other viruses, which, in turn, can download the actual ransomware.
Once downloaded, the ransomware can start executing and spreading laterally through the network, looking for critical system files and other sensitive data. After spreading through the network, it waits for an opportune moment where it can start encrypting these files, and upon reboot, the victims are presented with the ransom note.
At this point, the victim faces the dilemma of either giving in to the demands and paying the ransom to regain access to their data or refusing to pay the ransom and rebuilding their entire infrastructure from scratch. However, it is important to note that paying the ransom might not always lead to the recovery of all the files. In some cases, the damage is severe, and some files are never decrypted. It is also important to note that while the decisions are being made, heavy costs are incurred due to system downtime.
As the number of internet users increases, there has been an increase in the trend to encrypt data so that user and data privacy can be preserved. This trend has led to over 94 percent of the internet being encrypted. The security “blind spot” created by this encryption can render traditional network defenses useless, as they cannot inspected encrypted traffic.
Enabling decryption on existing, point solutions may not be a good idea as it can adversely affect the overall user experience and create bottlenecks in the network. You can read more about this approach here.
There are solutions out there that claim to let you inspect encrypted traffic without actually decrypting it. However, that approach fails on multiple levels throughout the timeline of an attack.
Only a dedicated decryption solution, that actually decrypts the traffic and enables other security devices to inspect it in clear text, can help protect you against hidden ransomware and other malware attacks.
With Ransomware, Prevention Truly is Better than the Cure
Ransomware is a highly dangerous attack that can devastate a network, bringing entire cities down to their knees. Even though, based on the recent trends discussed above, the future seems bleak, such attacks can be stopped by having a solid security plan in place. Security strategies should be carefully mapped out, focusing on the rising trend of targeted ransomware, and making sure the following points are taken into consideration:
- Raise awareness about social engineering and phishing attacks – As delivery via email attachments is one of the most common ways attackers deliver ransomware, make sure city employees are educated about the risks involved, and that they should report any suspicious emails/attachments before downloading or opening them.
- Back data up regularly – Sensitive data should always be backed up at regular intervals to secure systems so that in case of a ransomware attack, the recovery process can be carried out in a faster and more efficient way.
- Ensure security patches are applied regularly – Attackers are always on the look-out for vulnerabilities to exploit. These can be present on the network security devices, as well as endpoint systems or servers. To deny attackers this opportunity, make sure automatic upgrades are enabled and systems are regularly upgraded, as the vendors send security patches. Once applied, ensure that the systems are rebooted, and the patches applied are up and running.
- Invest in a dedicated decryption solution – To gain full visibility into encrypted traffic and to stop any hidden attacks at the network edge, make sure that you invest in a dedicated decryption solution. A decryption solution like A10 Networks’SSL Insight can enhance the efficacy of your existing security infrastructure and help stop attacks at any stage in their timeline, whether it’s a malicious file being downloaded, or an infected system trying to establish C&C communications.