What is Ransomware?
All Ransomware is Malware, but not all Malware is Ransomware
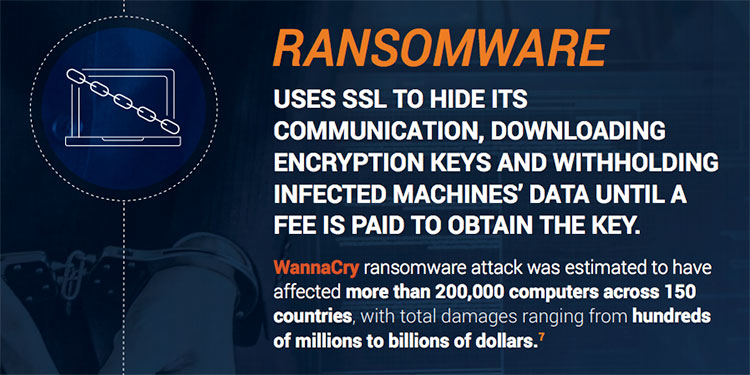
Ransomware is a type of malware that is spread by malicious payloads from deceptive links in phishing emails, drive-by content downloading from websites or other links in messages from text to Skype. The user is unaware of the ransomware infecting their computer until it’s too late and their system and/or files have been locked down via encryption. A decryption key is not shared with the victim until a ransom payment is sent, which can be as low as $200 for individuals or millions for enterprises, usually paid out in Bitcoins.
If the ransom is not paid, your only option is to wipe your hard drive clean and start from scratch. But ransomware payment doesn’t guarantee the victim will receive a decryption key and if it is, it doesn’t guarantee the ransomware will be removed. It could pop it’s head up again in the future or move on to infect other machines in the victim’s network.
Learn more about ransomware, phishing, zero trust, and the new normal of cyber security
“Paying the ransom does not guarantee the encrypted files will be released; it only guarantees that the malicious actors receive the victim’s money, and in some cases, their banking information. In addition, decrypting files does not mean the malware infection itself has been removed.”
– U.S. Cybersecurity and Infrastructure Security Agency
How A10 Networks Assists with Ransomware Protection
Effective ransomware protection depends on complete visibility into your network’s encrypted traffic, so hidden attacks are stopped at the network edge before they can even make it into the network. A10 Networks Thunder® SSL Insight (SSLi®) enables TLS/SSL decryption and SSL inspection to detect ransomware and other exploits hiding in encryption traffic. The solution also has additional preventive security features like URL Filtering and Application Firewall which can be used to block users from accessing known infected websites and applications.
< Back to Glossary of Terms