Beat Gaming Cheaters and DDoS Spoilers with Real-time Packet Watermarking
Gaming, for entertainment or gambling, seems to bring out the worst in the worst people. Cheaters leverage an ecosystem of nefarious tool developers to get a competitive edge with new ways to unfairly advance, obstruct competitors, or attack the hosting platforms.
How prevalent is the problem? A study by Irdeto provides some interesting insights into the issue.
60% of gamers have had their multiplayer gaming experience negatively impacted by other players cheating

Source: Irdeto Global Gaming Survey
Distributed Denial of Service (DDoS) defenders need new approaches to balance the operations in favor of fair and continuous play because everyone is watching, and no one wants to play on an unfair battlefield.
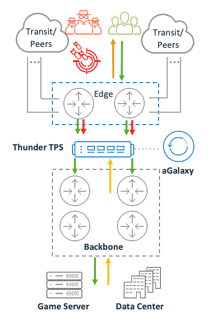
One approach to enhance the zero-trust defensive posture required for gaming platforms is to use real-time watermark inspection on all traffic from the internet to the gaming server. Time-based packet watermark checks at the network peering and transit edge give gaming operators the ability to ensure only legitimate gaming clients communicate with the gaming server. The challenge is having the performance to inspect every packet for a valid token without impacting the adrenaline-pumping game with energy-draining delays or abandon-worthy jitter.
How Watermarking Works
Time-sensitive tokens are generated by the game operator; one-way encoded to prevent algorithm discovery and then passed to legitimate clients. The client application will watermark each communication packet with the current token destined to the gaming server. Accesses without the token or with an expired token are blocked before it reaches the server.
Narrow the DDoS Weapons Available
Like everything in security, nothing is 100-percent guaranteed, but with packet watermarking, the attack surface is greatly diminished, while placing an additional burden on the bad actors to prevent a breach of the environment or mitigate DDoS attacks.
DDoS attacks have two delivery methods: reflected amplification attacks or direct botnet stateful/stateless attacks. Reflected amplification attacks leverage millions of publicly exposed servers (e.g., DNS, NTP, Memcached, etc.) that respond to an unauthenticated request with an amplified response toward the victim. It is called reflected because the attacker spoofs the IP of the victim as the requester. The amplified part comes into play because of the request, typically a small 64B packet, illicit and up to 51,000 times (Memcached) sized of a response. Whereas, botnet attacks leverage DDoS weaponized malware-infected computers and IoT devices under the control of a DDoS-for-hire service.
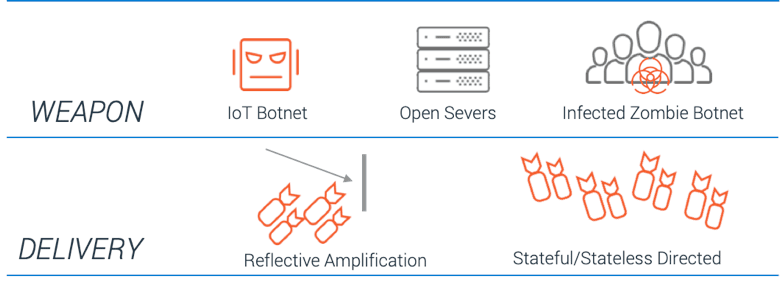
Packet watermarking-based DDoS defenses eliminate all types of reflected amplification attack effectiveness since none of these exposed servers used in reflected attacks will have the token or know-how to get the token off of the gaming platform. Nor is it likely that the botnet under the control of DDoS-for-hire services will see the token, as they will likely be IoT devices, not gaming client machines. That only leaves compute nodes that are under the control of an active user’s gaming network that could be used as a DDoS weapon.
Prevent PCAP Replay
DDoS attackers, like their legitimate player counterparts, are persistent and innovative. One strategy is to make DDoS traffic look like game traffic. This can be done by capturing packets off of their network interface card (NIC) and then replaying that traffic at a high rate or replaying it across a distributed botnet under the attacker’s control. However, tokens are commonly aged out in seconds or minutes, so the attack window is minimized. The token can also be locked to only a single session to eliminate noisy reuse of the token on additional gaming sessions.
Online gaming DDoS defenders, you have it rough. Your industry is the most frequently targeted by DDoS attacks, and often you’re attacked by your own users! Watermarking communication traffic is an effective way reduce the attack surface available to cheaters and DDoS spoilers.
A10 Networks provides advance techniques for gaming defenses including real-time per-packet watermark inspection, actionable DDoS weapons intelligence, five-level adaptive policy, and Zero-Day Automated Protection (ZAP). For more information on A10 Networks’ DDoS solutions, visit the DDoS Protection page.