How Zones Facilitate a Proactive DDoS Defense that Protects Real Users
The primary objective of DDoS protection is to ensure availability of services to legitimate users. Secondarily, protecting the service’s infrastructure from being overwhelmed aligns with safeguarding a user’s access. Sometimes, DDoS defenders miss the nuances of this priority because IT gets graded on a measurable five-nines uptime, but rarely on user experience.
When the user experience matters, a proactive in-path (L3 or L2) DDoS defense is most effective. An always-on proactive defense has the benefits of instant response to policy violators and packet-level application-layer visibility for full-spectrum multi-vector DDoS protection.
That said, proactive deployment cost is a primary concern for large networks because this defense strategy requires 1:1 defense capacity to total ingress traffic. This means that no over-subscription is possible like that found in flow-based reactive deployment. Other commonly stated concerns about implementing an always-on defense are false triggered mitigations and added latency caused by packet-level traffic inspection during peacetime.
Errors and latency are legitimate concerns for legacy DDoS defenses that have static policies manually activated or continuously present. Some equipment vendors recommend using a tap mode for packet-level detection. However, this is a non-intrusive POC evaluation technique and is rarely ever viable in production environments due being expensive and added complexity.
A10 Networks solves this problem through the use of user-defined adaptive five-level policies supported in its protected Zone construct. The adaptive escalation capabilities let the operator define up to five levels of mitigation rule sets that the Thunder® Threat Protection System (TPS) will step through during a DDoS attack. The first level (L0) is typically defined as peacetime with no mitigation rules applied and latencies measured in microseconds. During this phase, Thunder TPS is monitoring for swells in traffic across multiple traffic indicators of each defined Zone (up to 3,000 active Zones per device). Table one below shows the monitored traffic rate and ratio learned during peacetime and deviation tracked to determine wartime for TCP services within the Zone. Similarly, relevant indicators are supported for UDP, ICMP, IP and other protocols. Once any of these learned detection thresholds are violated, escalation occurs and next level-set of rules are applied to the Zone.
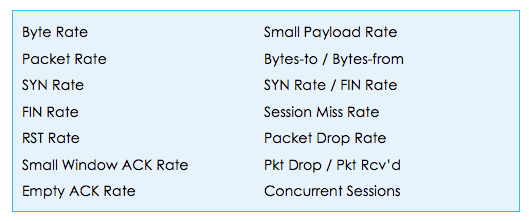
Table 1: TCP-based Service Tracked Traffic Indicators
Tracking more indicators than BPS and PPS adds detection effectiveness, especially for network- and application-layer attack detection. One, less understood, but handy indicator is Session Miss Rate. The name is confusing, but it tracks the number of new IP addresses seen. A wave of never-before-seen IPs is a good indicator of a DDoS attack or possibly a Flash Crowd. Either way, it is time for a more in-depth inspection.
Another important reason for using adaptive policies is that not all mitigation strategies are equal in protecting users. For example, RTBH and destination traffic shaping inherently and indiscriminatingly clears out traffic to protect the infrastructure, while leaving a wake of collateral damage against legitimate users. Adaptive policies let you sequence mitigation according to your unique network and application needs.
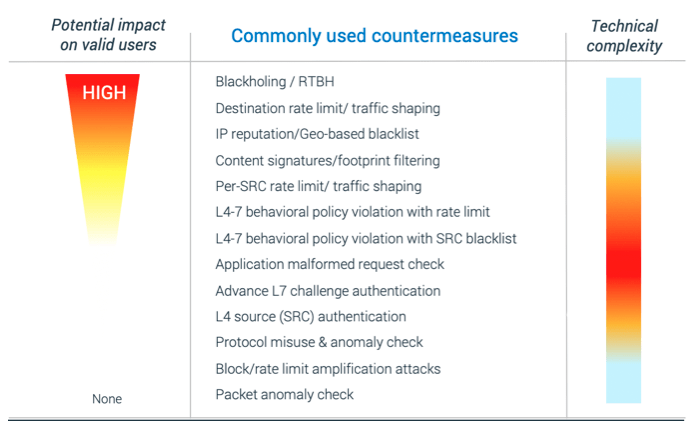
Figure 1: Sample of Mitigation Types
For example, you may apply reflected amplifier threat intelligence IP blocking and set generous source rate limits to squelch loud amplification attacks before tightening acceptable access rates, activate Zero-day Attack Pattern Recognition (ZAPR), and initiate botnet check; and then use destination traffic shaping controls as a last resort. The adaptive nature allows the defense operator to apply the right level of mitigation to the attack while minimizing damage to users whenever possible.
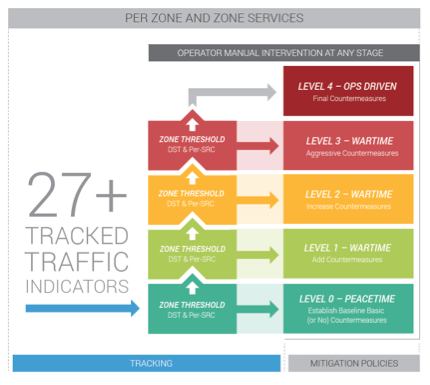
Figure 2: Adaptive Five-level Policy
Earlier, we mentioned Flash Crowds. By using adaptive policies, each real user will pass without breaking a policy until the crowd becomes too large, and infrastructure protection must kick in as a last resort.
Your workers and customers are the drivers for your business, so be kind to your most valuable resources. Leveraging adaptive techniques, you can accomplish five-nines uptime and discriminately protect your users while under DDoS attack.
For more information on A10 Networks’ DDoS solutions, visit the DDoS Protection page.