Boosting mobile revenue with 5G security-as-a-service

The transition to 5G will bring many opportunities to mobile service providers but it will also continue to challenge them to drive greater levels of subscriber revenue. The average revenue per user (ARPU) is flat to down while data volume per device is rapidly rising. Traditional pricing plans are being disrupted around the world and all-you-can-eat plans are expected. Substantial investment in infrastructure is expected to support this growing data volume. To remain profitable, service providers need to find new revenue streams.
They can explore new revenue streams by focusing on value-added services and reducing their reliance on just being a data-pipe. One such stream is providing security-as-a-service to reduce the risk facing the emerging new use cases. In fact, service providers might be able to, not only monetize their investments, but differentiate themselves via these value-added services and build a more sustainable and profitable business.
Usage booms—while ARPU lags
The growth of mobile data has reached truly explosive proportions. According to the Ericsson Mobility Report of June 2019, total mobile data traffic will reach 131 exabytes (EB) monthly by the end of 2024, a 30 percent CAGR from 2018. In North America alone, mobile data traffic will average 39 GB per month, per smartphone by that time, an increase of more than five times the average of 2018. To support this global rise, the GSMA expects mobile operators to invest around $480 billion worldwide between 2018 and 2020 in mobile CAPEX.
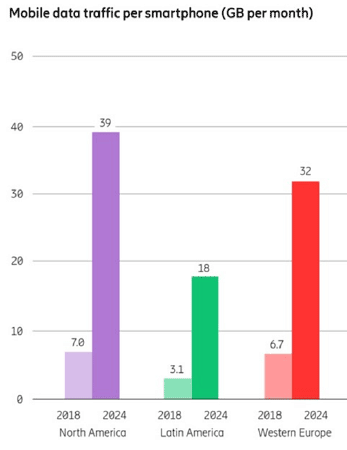
Source: Ericsson Mobility Report, June 2019
But judging from past experience, these massive investments will not necessarily bring correspondingly large returns. As noted in a study by Ericsson and Arthur D. Little in 2018, operators who invested in 4G upgrades quickly realized that while usage increased dramatically, revenue per user did not; the overall CAGR was only 1.5 percent. Simply put, consumers want to get more, but they don’t want to pay more. Competitive price pressures and the spread of all-you-can-eat data plans have left service providers without the leverage to raise rates, putting relentless pressure on margins.
In this light, it’s no wonder some service providers have been less than enthusiastic about investing in the move to 5G. Indeed, many operators have yet to recoup their investments in 4G infrastructure.
Rescuing revenue with value-added services
The solution to the mobile revenue squeeze is not to try to resist or delay the march of 5G; it’s to lean into the innovation 5G makes possible—and to monetize the security challenges it raises.
The GSMA describes the emerging economic model for mobile data in simple terms: “Connectivity will be commoditized; value generation lies in the applications, platforms, and services layer.” This statement comes in the context of a discussion of the Internet of Things (IoT), but this is only one of the diverse use cases that will drive massive growth over 5G networks. A recent survey commissioned by A10 Networks found smart cities, industrial automation, ultra-high-speed connectivity, and connected vehicles to be key use-case drivers for 5G, to name just a few. Remote surgery will transform healthcare. Augmented reality and virtual reality, powered by AI and cloud computing, will disrupt the retail experience. Rural and otherwise inaccessible areas will finally see the potential for ubiquitous high-speed connectivity.
To enable this transformation, 5G connectivity is increasingly being complemented by multi access edge computing (MEC), an architecture in which applications are moved out of traditional on-premises and cloud data centers to the network edge to speed performance and reduce network latency.
It is this shift, and its implications for the viability of 5G-enabled value-added services, that creates the opportunity for differentiated security services.
From dumb pipes to smart security
Even before considering the impact of 5G MEC architecture, the explosion of new devices coming online vastly increases the security challenge facing enterprises and other service providers. According to the GSMA, between 2018 and 2025, the number of global IoT connections will triple to 25 billion. As the attack surface expands exponentially, service providers will have to ensure that malware, intrusions, DDoS attacks, and other threats don’t disrupt the delivery of 5G services. This is even more critical given the literally life-and-death nature of services like remote medicine and driverless and connected cars.
Add MEC to the picture, and the challenge grows still greater. As applications move from the data center to the edge, they become more vulnerable to cyber attack. With more limited compute resources at an edge micro-data center than a traditional enterprise or cloud data center, a DDoS attack can bring down an application much more quickly and easily.
To protect these new use cases, including services and applications provided by their enterprise customers, mobile operators can now step in with new security-as-a-service offerings such as DDoS detection, Layer 4/Layer 7 firewall, GTP/Diameter/TLS (Transport Layer Security) inspections, HTTP protection, and IPSec VPN. By protecting businesses and customers from degraded performance, unavailability, fraud, data breaches, and other risks, service providers can move beyond commodity connectivity to deliver greater value—and charge accordingly.
With the 5G revolution already well underway, mobile service providers face unprecedented urgency to bring their revenue in line with their costs. By capitalizing on the opportunities for value-added services created by 5G—and by creating new security services to protect those use cases—operators can rebuild their economic model for a new era of profitability.