Combating the Siege of Multi-Vector DDoS Attacks

For the past year, you’ve surely heard about multi-vector distributed denial of service (DDoS) attacks getting bigger, badder and more sophisticated.
You’ve undoubtedly read the headlines about the Mirai botnet fueling colossal DDoS attacks and WireX turning smartphones into weaponized DDoS devices.
The DDoS threat landscape is changing; this much is obvious. But how is it changing? How is this explosion of DDoS activity affecting businesses? What’s happening in the real world? And what can we learn from this shift so we can better protect ourselves against DDoS attacks? Because, let’s face it, there is such a thing as bad press, just ask any of the victims who have suffered downtime at the hands of a widely publicized DDoS attacks.
Digging Into the DDoS Attack Data
A10 Networks commissioned IDG Connect to conduct a survey that uncovered the truth about the evolution of DDoS attacks. Here we’ll look at some of that data. This is just a glimpse.
Growth of DDoS Attacks
The gargantuan 1 Tbps attacks that started last year with the Mirai botnet make up a fraction of the DDoS landscape – two percent of respondents say the average size of DDoS attack their businesses face is 1 Tbps or more. That may sound small on the surface, but when compared to two years ago, it’s a startling difference. A similar survey conducted in 2015 found zero accounts of attacks of 1 Tbps or higher.
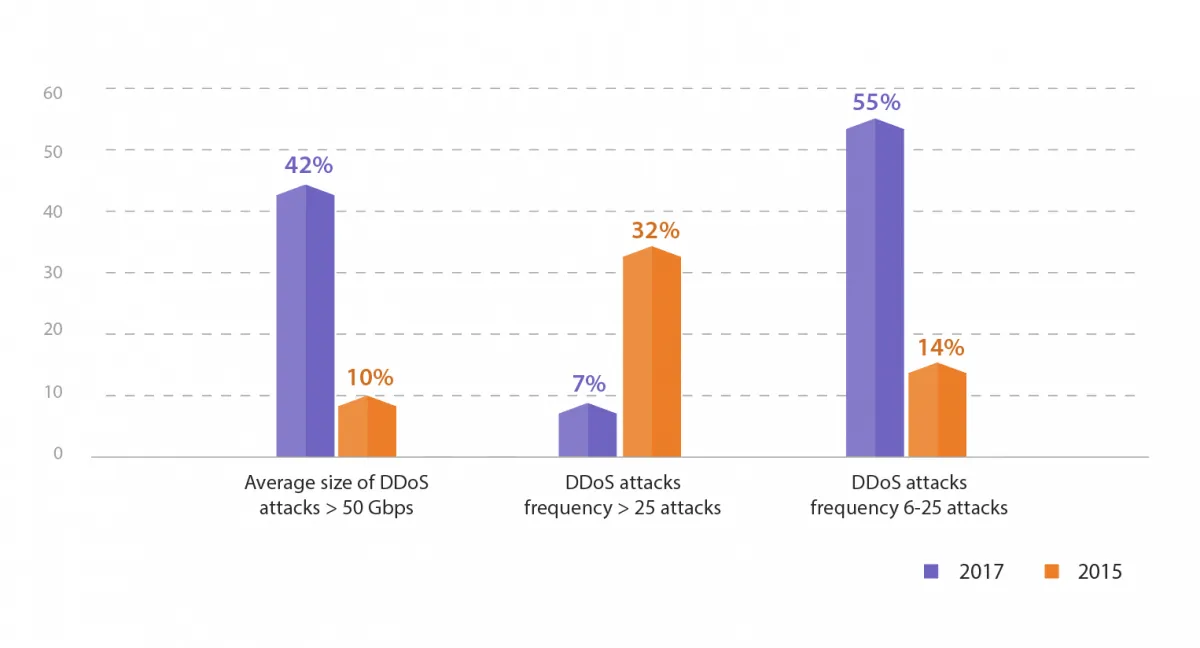
At the same time, data from 2015 shows that only 10 percent of respondents noted attacks of more than 50 Gbps. Today, 42 percent of respondents have seen attacks of 50 Gbps or more – that’s an increase of more than four times since 2015.
Attacks From All Sides
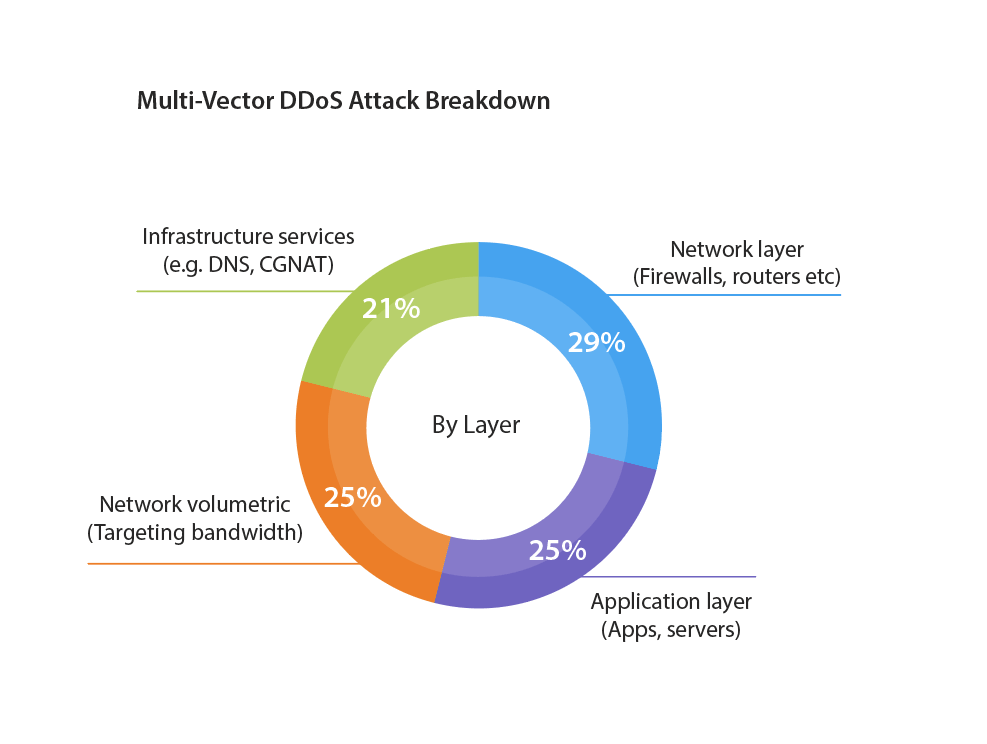
We also asked respondents what percentage of multi-vector DDoS attacks their businesses have experienced. The results show the types of multi-vector DDoS attacks businesses face are spread fairly evenly across four categories. Network layer DDoS attacks targeting network components like firewalls and routers lead the charge, with 29 percent of respondents saying their business ran into them. That’s followed closely by application layer attacks that target applications and servers (25 percent), network volumetric attacks targeting connectivity bandwidth (25 percent) and infrastructure services attacks against services like DNS and CGNAT (21 percent).
DDoS Attack Downtime is Down
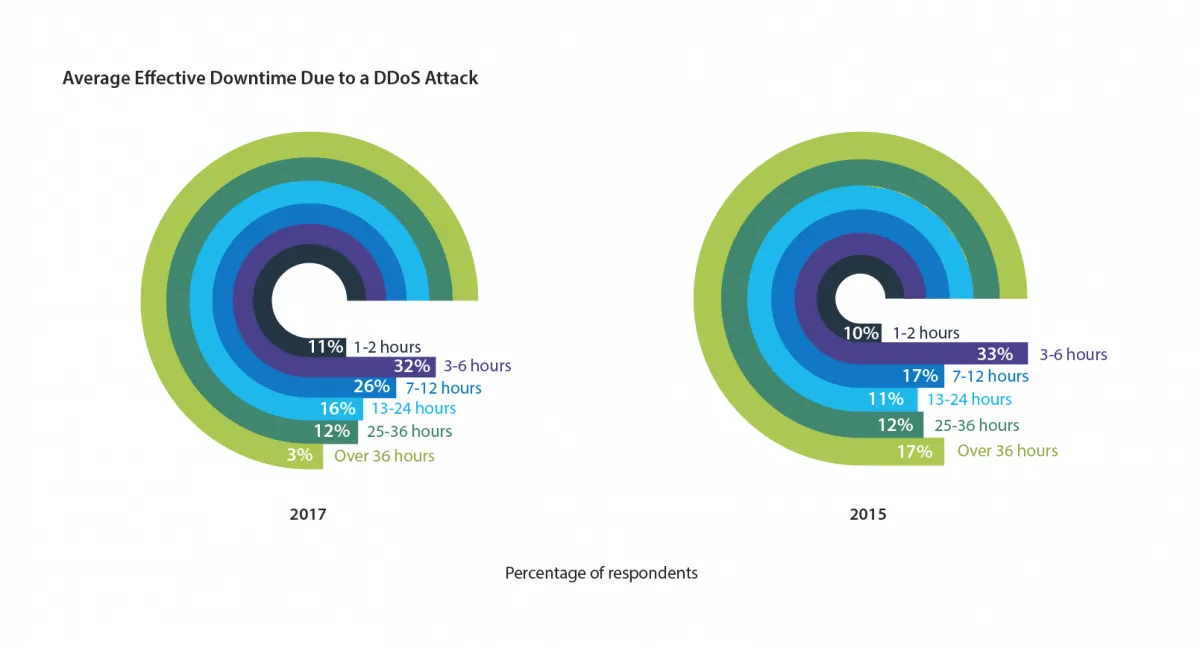
Doom and gloom aside, there’s a silver lining in the DDoS landscape, and that’s due to attack mitigation and remediation solutions shrinking the amount of downtime caused by attacks. For example, only 3 percent of respondents say the average effective downtime they suffered due to a DDoS attack is more than 36 hours, compared to 17 percent two years prior. And the majority of respondents (32 percent) say the average downtime is three to six hours, which is one percentage point lower than 2015.
Customer Satisfaction First
Customer satisfaction is now the main measurement of the impact of downtime. Eighty-six percent of respondents say customer satisfaction is the main metric they use to determine how downtime affects their business. That’s followed by time to service restoration and the amount of time that order processing is offline (both with 82 percent). Customer satisfaction rose 20 percentage points in two years, showing that businesses are paying closer attention to overall customer experience and the customer is in the driver’s seat.
Effective DDoS Defense Is a Must
As multi-vector DDoS attacks continue to increase and assault networks and applications, organizations need the highest-performing DDoS detection and mitigation to identify attack traffic and eliminate it. Respondents note that throughput performance and multi-vector protection metrics are the most important benefits they seek in a new DDoS solution.
That’s where A10 Thunder® Threat Protection System (TPS™) comes in.
Thunder TPS delivers the industry’s best scale with up to 300 Gbps at a rate of 440 Mpps. And it can detect and mitigate attacks of all sizes, from megabit- to terabit-sized DDoS attacks. Additionally, Thunder TPS tracks more than 27 traffic behavioral indicators against learned peacetime traffic to detect anomalous behavior and surgically distinguish legitimate users from attacking bots.
All of this means that your business is better protected from DDoS attacks and the damaging downtime they cause. And that results in happy customers, which, as the survey found, is crucial.
To dig deeper, in the full report you’ll find all the latest DDoS trends regarding:
- The biggest barriers to preventing a DDoS attacks
- The frequency of attacks
- The most preferred DDoS solution
- The most effective DDoS feature
- Forecast and budget allocation
You can find this and much more in the full report, which you can download here: A10 IDG DDoS report.
And for more information on A10 Thunder TPS, download our data sheet.
Seeing is believing.
Schedule a live demo today.