Millions of DDoS Weapons Used for Volumetric and Sophisticated Attacks
In the recently published DDoS weapons report, A10 Networks describes the geographic and organizational concentration of the 12.3 million bots and amplifiers—the weapons that cybercriminals can use to launch increasingly bigger, more complex and less detectable DDoS attacks against any organization or service provider from anywhere in the world. AI tools and automation techniques are increasing cyberattack efficacy while decreasing the cost and risk to the cybercriminals using these weapons. For enterprises and service providers, DDoS protection of networks, web sites, APIs and other digital assets is critical to business continuity, and security teams fight an ongoing battle to maintain adequate cybersecurity investment against growing cybercriminal expertise.

Today, volumetric attacks exceeding multiple terabits per second (Tbps) are not uncommon and utilize any of the 12 million+ amplifiers scattered across the globe, spoofing IP addresses and making detection of the attack source difficult. For example, in April 2025, a hyper-volumetric, multi-vector attack was reported at 6.5 Tbps and 4.8 billion packets per second. This attack used more than 30,000 unique IP addresses (weapons) from 147 countries and multiple attack vectors, including SYN flood attacks, Mirai botnet, SSDP amplification, CLDAP and ESP reflection/amplification.
As discussed in the report, amplifiers are created from a deep pool of lightly protected IoT devices or other misconfigured network elements that are “open” on the internet and thus vulnerable to cyber intrusion. The organizations hosting these weapons are often unsuspecting victims and are not aware that their devices have been compromised and are being used in attacks. Heavier concentration of weapons is found in countries with larger quantities of connected devices (e.g., China and the U.S.), but weapons can be drawn from anywhere in the world for use in a DDoS attack.
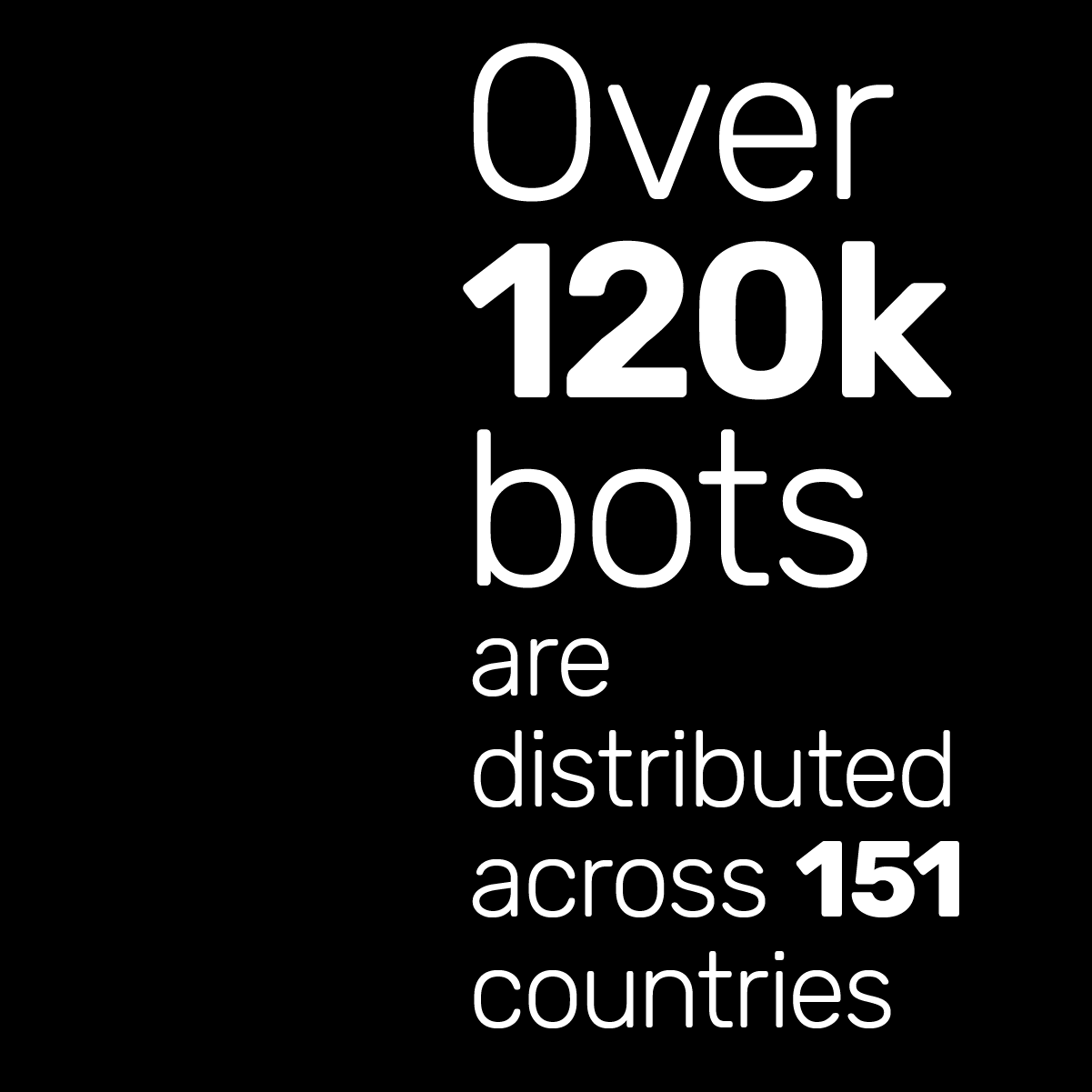
Bots also play a role in DDoS attacks and are responsible for recruiting and activating the millions of amplifier weapons. In the 2025 sample discussed in the report, A10 identified over 120,000 bots distributed across 151 countries and hundreds of organizations. As a region, Asia hosts 89 percent of tracked DDoS bots globally, with 80 percent of global bots hosted in China and India. Botnets, such as Mirai, continue to evolve and grow with over a hundred variants now recognized.
State-sponsored actors and grassroots hacktivists use DDoS weapons to launch network-layer attacks that disrupt service to critical infrastructure and government agencies, and are often politically motivated by events, such as the ongoing war in Ukraine and the 2024 national elections in the U.S., Taiwan, India and the United Kingdom.
Enterprises are more typically targeted for monetary gain or to acquire valuable customer credentials. While massive volumetric, network-layer DDoS attacks continue to create headlines, sophisticated and subtle application-layer attacks (Layer 7) are often a greater security challenge for organizations. They exhaust application resources (CPU, memory, threads) at API gateways, DNS, web and HTTP services, often flying below traditional detection thresholds.
In a prior blog post, we provided details on DDoS attacks over the years, including the most well-known. Here is a summary that shows the steady progression of DDoS attacks, using the weapons in the 2025 DDoS weapons report.
- 2025 – Application-layer DDoS with Credential Stuffing: In an example attack, A10 ThreatX team mitigated an API attack against a large financial services organization. The attack generated a high volume of HTTP/2 requests, spoofing legitimate mobile applications with authentic-looking user agent strings. The attack included 49k requests on 198 customer web sites from over 13k unique IP addresses and 121 countries. Mitigating the attack utilized forty-four different rules. The attack illustrates the shifting tactics of cybercriminals to combine DDoS with other attack vectors, and the higher level of sophistication required for mitigation.
- 2023 – Emergence of HTTP/s Rapid Reset: Record-breaking DDoS attacks against AWS, Google, Cloudflare used significantly smaller botnets than previously seen. The attack exploited a feature in HTTP/2 that allows for rapid request cancellation using the RST_STREAM frame, which can eventually overwhelm servers by continuously opening and closing streams, leading to resource exhaustion.
- October 2020 – 2.5 Tbps Google Attack: The attacker used several networks to spoof 167 Mpps to 180,000 exposed CLDAP, DNS, and SMTP servers. This demonstrates the volumes a well-resourced attacker can achieve. This was four times larger than the record-breaking 623 Gbps attack from the Mirai botnet a year earlier.
- February 2020 – 2.3 Tbps AWS attack: Targeted an unidentified AWS customer using CLDAP reflection. This technique relies on vulnerable third-party CLDAP servers and amplifies the amount of data sent to the victim’s IP address by 56 to 70 times. The attack lasted for three days.
- February 2018 – 1.35 Tbps GitHub Attack: GitHub was hit with a DDoS attack that lasted 20 minutes. According to GitHub, the traffic was traced back to “over a thousand different autonomous systems (ASNs) across tens of thousands of unique endpoints.”
- Sept – Oct 2016 – 620 Gbps to 1.1 Tbps – Multiple Mirai attacks: The Mirai botnet, which at its peak in 2016, consisted of over 600,000 compromised IoT devices such as IP cameras, routers, and video players.
- September 2016: Brian Krebs’ cybersecurity blog hit by Mirai.
- October 2016: OVH hit with 1.1 Tbps attack.
- October 2016: DNS provider Dyn hit with 1.5 Tbps attack.
- Mirai ecosystem is now fragmented into hundreds of botnets and continues to exploit new IoT vulnerabilities.
The large pool of 12.3 million DDoS weapons available to cybercriminals is examined in detail in the 2025 DDoS weapons report. These weapons are used in massive attacks and also as part of more complex, stealthy campaigns that require greater enterprise vigilance and security investment. Simple volumetric mitigation is no longer adequate.
