Why DDoS Attackers Love Companies with Multiple Data Centers

In the eyes of DDoS attackers, the more data centers a company has, the more of a gold mine it is: In the 2018 IDG DDoS Report, we found that companies with multiple data centers experience larger and more frequent attacks than those with fewer data centers.
But why are data centers such optimal targets for DDoS attacks, and what types of attacks are they most susceptible to? Read on to find out.
Companies With >5 Data Centers Are Prime Targets
As mentioned above, companies with several data centers experience more DDoS attacks than other companies, and the attacks against them are typically much larger than those against companies with fewer data centers.
It’s important to note that this difference in DDoS attack size and frequency is far from insignificant.
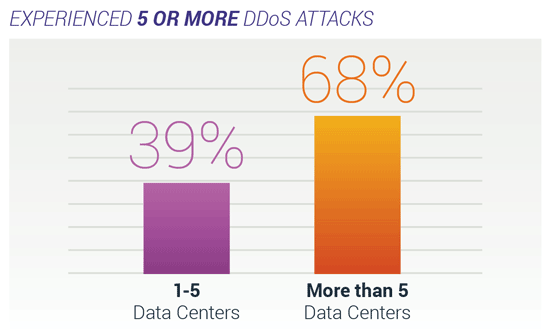
Sixty-eight percent of companies with five or more data centers have experienced five or more DDoS attacks, compared to 39 percent of companies with one to five data centers. That’s a difference of almost 30 percent.
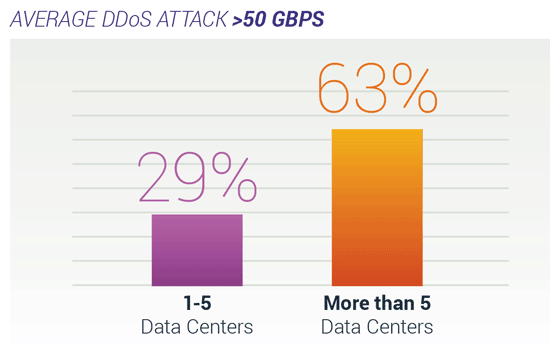
Similarly, 63 percent of companies with five or more data centers experience DDoS attacks with an average size of 50 Gbps or greater, compared to 29 percent of companies with one to five data centers. That’s a 34 percent difference.
Why More Data Centers = More DDoS Attacks
Why this stark discrepancy in frequency in size? It all comes down to ease of access.
Think of it this way: If a bank robber found a bank with multiple vulnerable vaults in multiple locations, it would be much easier for them to rob the same bank again and again than it would be for them to find a new bank.
Plus, a bank with many vaults holds more money than a bank with just one.
The same principle applies to DDoS attackers. Once an attacker has identified a vulnerable target with several different data centers that are all ripe for the picking, they’re likely to keep repeatedly targeting that same group of data centers.
Plus, companies with multiple data centers will likely struggle to fully implement new security measures between subsequent DDoS attacks. This presents an ideal opportunity for attackers to exploit a company’s lack of comprehensive security over and over again.
Unfortunately for those companies, data center downtime can be financially devastating.
According to research from the Ponemon Institute, the overall average cost of data center outages was a staggering $740,357 in 2016, compared to $505,502 in 2010 — an increase of about 46 percent. Using those numbers, we can estimate that the average cost of a data center outage in 2019 is more than $1 million.
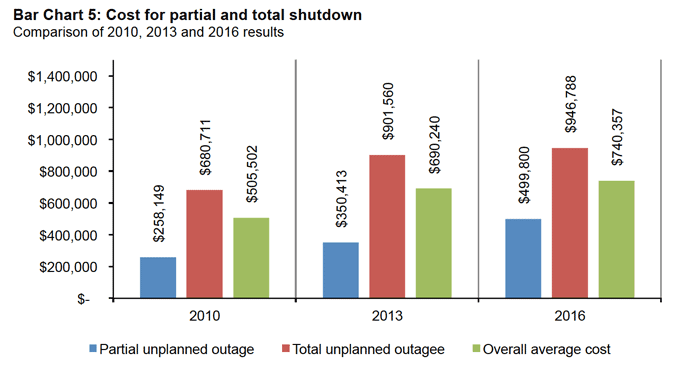
Small- and medium-sized businesses (SMBs) aren’t exempt, either: A 2017 survey from Information Technology Intelligence Consulting found that just one hour of downtime costs $100,000 for 47 percent of SMBs in any industry.
The IDG DDoS Report revealed that 36 percent of companies with more than five DDoS attacks experience 7-12 hours of downtime, and 34 percent of companies with less than five DDoS attacks experience at least one hour of downtime.
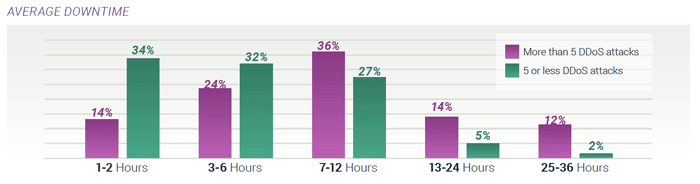
Knowing this, it’s clear that DDoS attacks can cause a significant loss of revenue for a great number of organizations.
Most Common Types of DDoS Attacks
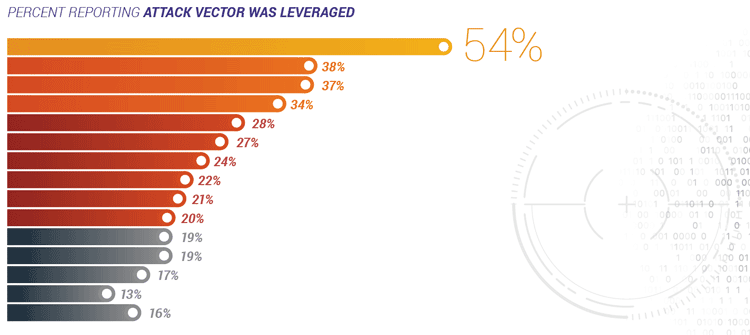
While the frequency of all types of DDoS attacks has risen significantly since the previous IDG DDoS Report, UDP flood attacks are leading the way by a large margin.
These types of attacks occur when perpetrators send massive numbers of packets to random ports, with each packet containing User Datagram Protocol (UDP) datagrams.
Such attacks represent 54 percent of DDoS attacks, while UDP fragment attacks take second place with a 38 percent share.
UDP fragment attacks are similar to UDP flood attacks except the packets being sent are fragmented, meaning that they’re bigger than normal packets. This allows attackers to achieve similar results with fewer packets.
Given that UDP packets flow directly through the data center, companies with multiple data centers are particularly vulnerable to the most popular types of DDoS attacks.
To successfully defend themselves, companies need to first be aware of the risks associated with having multiple data centers. Then, they must identify solutions — ideally on-premises — that can provide the comprehensive DDoS protection they need.
To learn more about the complex threats faced by companies today, as well as find out how you can better protect your organization, read the full 2018 IDG DDoS Report here.
Learn more about A10’s DDoS detection and mitigation products.
Seeing is believing.
Schedule a live demo today.