IoT and DDoS Attacks: A Match Made in Heaven

By 2020, Gartner predicts the total number of IoT devices will reach 20.4 billion. At the same time, DDoS attacks are on the rise, with Cisco estimating that the number of DDoS attacks exceeding 1 gigabit of traffic per second will soar to 3.1 million by 2021.
This is no coincidence: IoT devices are a common thread in large-scale DDoS attacks.
While we’ve covered this issue before, our Q4 2018 State of DDoS Weapons report sheds additional light on the connection between IoT and devastating DDoS attacks.
Here, we’ll go over some highlights of the Q4 2018 The State of DDoS Weapons report’s findings to expose the role that IoT plays in one of the biggest cybersecurity threats of our time.
An Overview of DDoS Attacks and IoT
It comes as no surprise that IoT is continuing to grow at breakneck speed: A 2018 report from Bain found that the combined markets of IoT will reach $520 billion in 2021, more than double the amount spent in 2017.
According to our own calculations, that translates to a growth rate of 127 connected devices per second, a number that will undoubtedly grow over the coming years.
Unfortunately, this IoT explosion also provides attackers with a perfect opportunity to hack into vulnerable connected devices, especially for the purpose of building botnets (networks of malware-infected connected devices that can be used to send an overwhelming number of requests to the target’s server).
As Eurecom discovered, hackers have already developed brand new strains of malware designed to target IoT devices specifically. Knowing this, it’s clear that the age of IoT-based DDoS attacks isn’t just on the horizon — it’s already here.
Some of the top IoT malware dropped have already reached global levels of infamy. Take for example the Mirai botnet, which brought major websites like Reddit and Github to their knees.
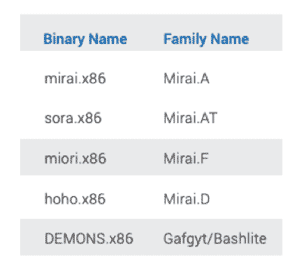
In our Q4 2018 State of DDoS Weapons report, we found that five of the top IoT malware dropped belong to the Mirai family, with the sixth belonging to the Gafgyt/Bashlite family.
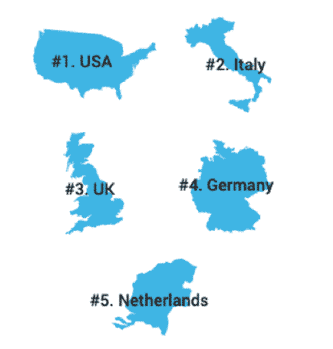
The majority of those malicious IoT items are hosted in the U.S., Italy, the U.K., Germany and the Netherlands.
In terms of ASNs, the majority of IoT malware is hosted by Frantech, DigitalOcean, Aruba, Forthnet and HOSTiO.

IoT DDoS Attacks and 5G
The increasing size of DDoS attacks today is bad enough, but things are about to get worse with the widespread adoption of 5G.
That’s because the implementation of 5G will usher in an age of unprecedented data speeds and significantly lower network latency, meaning that DDoS attacks will have to be mitigated in a matter of seconds, not minutes.
With Ericsson estimating that the number of IoT devices with a cellular connection will reach 4.1 billion by 2024, it’s plain to see why vulnerable 5G-connected IoT devices will pose a serious threat to organizations around the globe.
If left unchecked, the scale of 5G-connected IoT DDoS attacks is likely to make even the biggest attacks of today pale in comparison.
To combat the next generation of 5G DDoS attacks, it’s imperative that organizations implement advanced DDoS threat intelligence that combines real-time threat detection and automated signature extraction.
Only then can organizations effectively defend themselves against the colossal, hyper-fast DDoS attacks of the future.
Want to learn more about the latest DDoS weapons, how they’re being used and how you can protect yourself against them? Download our latest State of DDoS Weapons report now.
Learn more about A10’s DDoS Protection solutions.
Seeing is believing.
Schedule a live demo today.