ThreatX by A10 Networks
Web application protection across cloud, on-prem, and hybrid environments
Benefits of ThreatX
Flexibly deploy one unified solution that can cohesively protect your application ecosystem against attacks and attackers
Key Features
Unified Platform
Protect the application ecosystem with a single, integrated solution combining WAF, API, bot, and DDoS protection. Simplify deployment and minimize tool sprawl with one cohesive defense platform
Managed SOC
Gain continuous protection from the ThreatX SOC team, which monitors, validates, and responds to evolving threats in real time, minimizing false positives and reducing the team’s workload
API Protection
Secure all N-S requests–normal, malicious, business logic attacks–toward APIs within the deployment domain of ThreatX using behavioral analytics, fingerprinting, and cataloguing
Bot Protection
Defend applications against bot-based attacks like credential stuffing or scraping without disrupting legitimate users
Web Application Firewall
Accurately protect applications from advanced attacks like OWASP Top 10 without manual tuning
Layer 7 DDoS Protection
Maintain application uptime against multi-vector, advanced Layer 7 DDoS attacks that are disguised as normal traffic with Hacker Mind’s entity/transaction-based tracking, behavior-based detection and dynamic response
Product Demo
Watch ThreatX in Action
ThreatX provides a user-friendly UI with intuitive dashboards, detailed logs, custom rule generation, API cataloguing, and more.
Follow Carlo Alpuerto, sales engineering manager at A10 Networks, as he demonstrates the ThreatX capabilities that protect against threats like DDoS, bots, and more.
Frequently Asked Questions
Don’t see your question listed? Contact a product expert to get answers.
ThreatX takes a unified WAPP approach, holistically securing the entire application ecosystem from both attacks and attackers with the ThreatX SOC on top to further streamline usage of the tool.
Powered by Hacker Mind, ThreatX correlates behaviors across attack vectors, tracks by entity/transaction, and uses battle-tested algorithms to create an adaptive risk score, resulting in fewer false positives and the ability to dynamically detect and mitigate advanced threats. ThreatX is both flexible and adaptable. It deploys in an existing environment and creates custom policies based on specific needs.
Deployment is flexible—on-premises or SaaS-based. ThreatX sensors are fast and easy to deploy, on-boarding sites in hours. Leverage simplified dashboards that make it easy to focus on the most important, high-risk activity targeting APIs and apps.
Hacker Mind is the decision engine that powers ThreatX. It uses battle-tested ML algorithms, cross-vector correlation, and entity/transaction-based tracking to create adaptive risk scores.
The ThreatX SOC is a team of security experts that manages everything within the ThreatX solution suite. By leveraging the managed SOC, organizations experience an enhanced understanding of their security posture, without adding any extra workload on the internal security team.
The SOC team from ThreatX provides:
- Faster threat detection and lower false positives
- Continuous protection
- Outstanding time-to-value
- Provide tuning and policy enhancements, as needed
- Improved customer experience and service uptime
- Detailed logs and reporting for compliance requirements
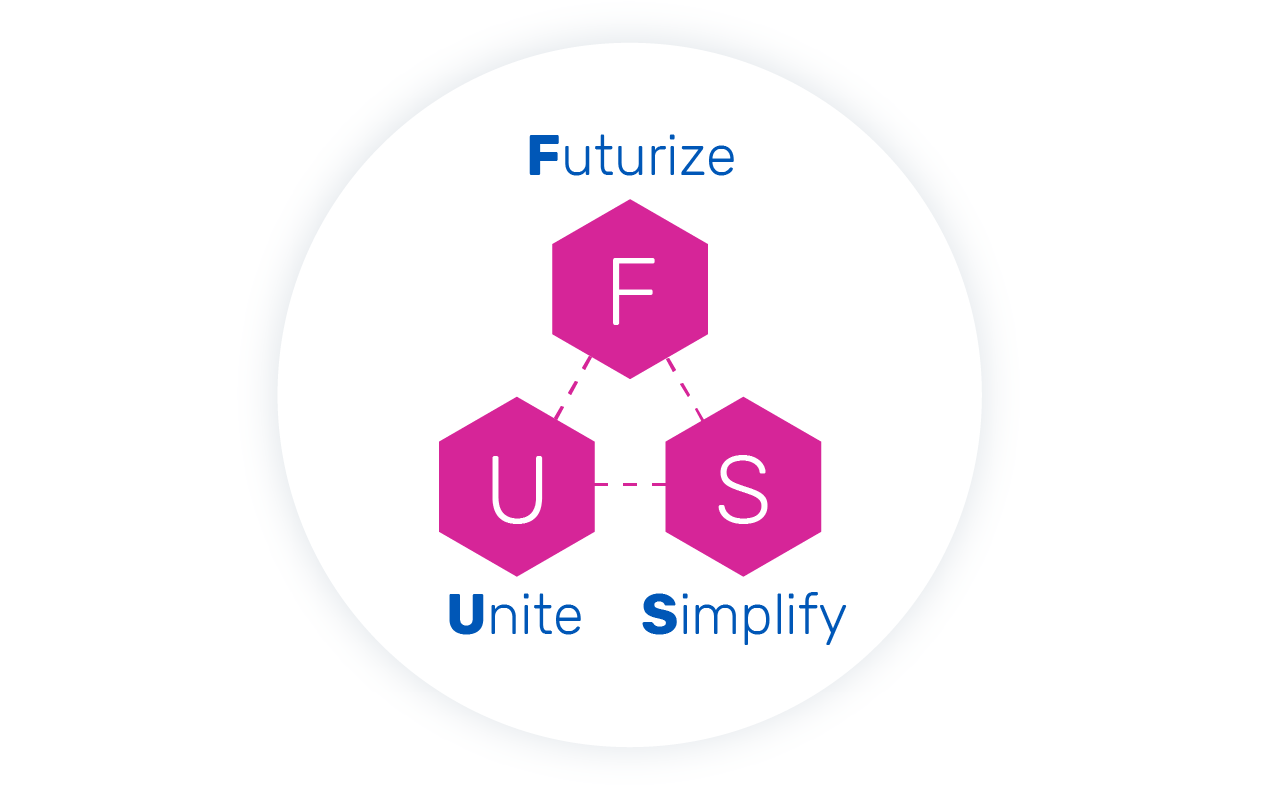
Futurize, Unite, and Simplify (FUS) the Protection of your Application Ecosystem
ThreatX unites protection across API, web, bot, and DDoS into a unified platform, a web application protection platform. Here’s how:
- Futurize: ThreatX leverages advanced ML, behavioral learning, and risk-based profiling to stay ahead of attackers.
- Unite: Instead of siloed defenses, ThreatX correlates activity across attack vectors and uses the information cohesively to adjust detection and mitigation strategies.
- Simplify: Instead of buying a WAF, then tacking on API protection, and then layering on bot and DDoS defense, ThreatX delivers protection in a unified platform.
What Customers Are Saying
Razor sharp technology right at your finger tips.
“The ability to block malicious threats and protect our business data was a great way to grab our attention. We love this product.”
Taking web app and API protection to a next level.
“This is a product that has given me high visibility on the attacks happening which has created a new level of understanding on the types of attacks that have helped my organization protect against those.”
A simple yet robust WAF solution that you should definitely look into!
“The best feature is it’s simplicity. Onboarding a new web application takes minutes. Everything about it’s interface is intuitive to use. If you do have to read their documentation, it is laid out very well and easy to understand.”