How the Best Communication Service Providers Thwart DDoS Attacks

We’ve already established that communication service providers (CSPs) are highly vulnerable to DDoS attacks.
In our previous post, we learned that 85 percent of CSPs say DDoS attacks against their organization are either increasing or maintaining their pace.
But what can CSPs do to protect themselves against the relentless waves of DDoS attacks they face?
That’s what we’re here to find out with the help of the Ponemon Institute’s 2019 report sponsored by A10 Networks, “The State of DDoS Attacks Against Communication Service Providers.”
The report revealed that high-performing CSPs who are successfully thwarting DDoS attacks know that:
- IoT devices are particularly vulnerable.
- Expansive threat intelligence is a must.
- DDoS scrubbing is a win for everyone.
Let’s take a closer look at each of those statistics to discover exactly how the best CSPs are staying one step ahead of DDoS attackers.
What Is a High-Performing CSP?
Before we get started, let’s clarify what constitutes a high-performing CSP.
When we talk about high performers, we’re referring to the 29 percent of survey respondents who say their organizations have a high level of ability to detect and mitigate DDoS attacks.
By comparing that group of high performers to the overall sample, the report found that CSPs who are highly capable of DDoS mitigation are also more capable of DDoS prevention and detection.
Specifically, 51 percent of high performers are effective at preventing DDoS attacks, compared to 34 percent of the overall sample.
Similarly, 55 percent of high performers are effective at detecting DDoS attacks, versus 39 percent of the overall sample.
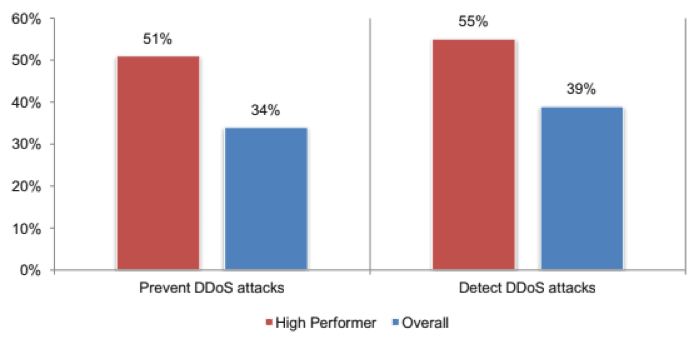
So, when we talk about high performers, we’re not just talking about CSPs that are good at controlling the impact of DDoS attacks—we’re talking about CSPs who are able to prevent and detect DDoS attacks, too.
Smart CSPs See the Risks of IoT
Here at A10 Networks, we’ve always seen why IoT devices are especially vulnerable to DDoS attacks (read our previous blog post here to learn more).
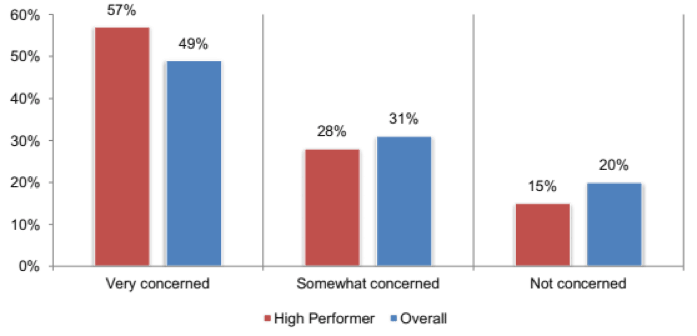
As it turns out, high-performing CSPs think much the same way, with 57 percent reporting that they’re “very concerned” about Mirai-type attacks that mobilize IoT devices (only 49 percent of the overall sample said the same).
In keeping with that, the greatest percentage of high performers (63 percent) say that IoT devices are the greatest DDoS-related security risk.
Comparatively, the greatest percentage of the overall sample (63 percent) named a lack of system connectivity and visibility.
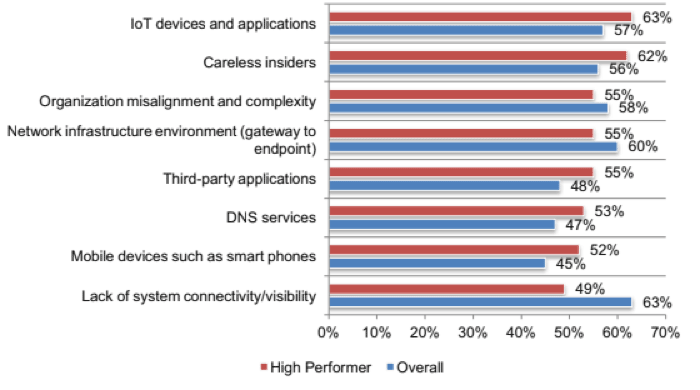
The takeaway: Just because IoT devices aren’t part of CSPs’ network infrastructure doesn’t mean they don’t pose a massive potential threat. All CSPs need to be aware of their vulnerability.
Comprehensive Threat Intelligence Is Crucial
Another distinguishing feature of high-performing CSPs is the level of importance they place on threat intelligence.
High performers’ threat intelligence differs from that of the overall sample in multiple ways:
- Fifty-six percent of high performers have threat intelligence, which includes information about DDoS-for-hire botnets, compared to 47 percent of all respondents.
- Fifty-one percent of high performers have threat intelligence, which includes reflected amplification weapons locations, compared to 44 percent of all respondents.
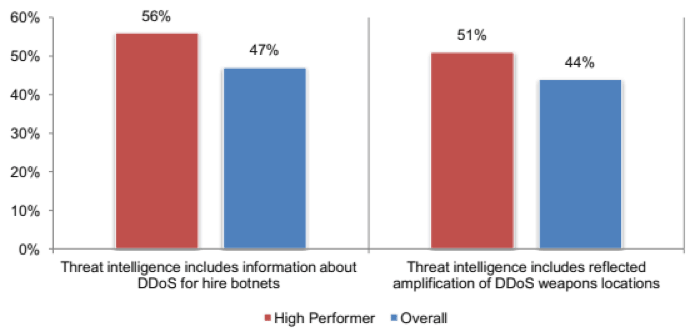
Given that both botnet and reflected amplification attacks are common, it’s not surprising that CSPs who have access to information about the weapons used in those types of attacks are better at detecting, preventing and mitigating DDoS attacks.
One thing that both high performers and the overall sample have in common, though, is their struggle to obtain up-to-date and relevant threat intelligence.
According to the report, the largest percentage of both high performers and the overall sample—61 percent and 70 percent respectively—agree that their DDoS-related threat intelligence is often too stale to be actionable.
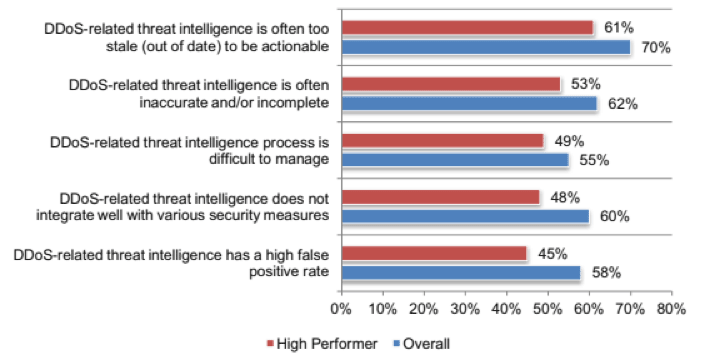
The takeaway: High-performing CSPs have access to threat intelligence with information about both DDoS-for-hire botnets and reflected amplification weapons locations. However, they still struggle to obtain truly actionable intelligence.
DDoS Scrubbing Has Major Benefits
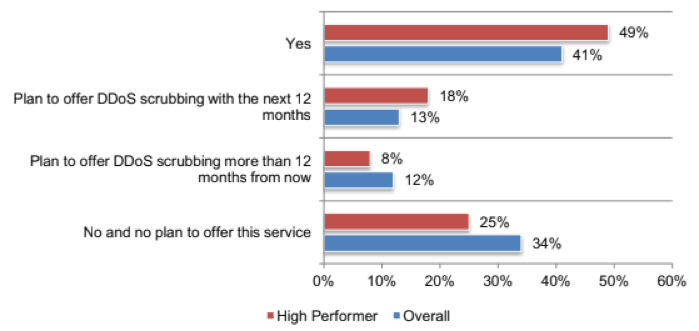
One of the report’s major findings was that 75 percent of high-performing CSPs either currently offer DDoS scrubbing services to subscribers or plan to within the next 12 months.
By comparison, the same is true for 66 percent of the overall sample — that’s a difference of nearly 10 percent.
It’s important to note that CSPs who offer DDoS scrubbing services stand to reap several benefits:
- Increased revenue opportunities
- Enhanced customer loyalty and trust
- Fewer subscriber support tickets
As a result of those benefits, the decision to offer DDoS scrubbing services isn’t just a good idea in terms of security. It’s also a boon to business.
The takeaway: CSPs who offer DDoS scrubbing services won’t just enjoy stronger security for themselves. They’ll also be able to pass on those advantages to their customers.
In the end, all CSPs could stand to be more resilient against the ever-growing onslaught of DDoS attacks. By heeding the lessons unearthed in this report, they just might be able to.
To find out more about how top-performing CSPs are successfully defending themselves from DDoS attacks, read the full report here.
Seeing is believing.
Schedule a live demo today.