Fast and Secure Microsoft Exchange Deployment
Email System Architecture
Email is one of the most commonly used and visible services provided by an IT department. Half the world’s population uses email. There will be over 4 billion email users creating 320 billion emails per day by 2021.
An email system consists of the following main components:
- Directory service to lookup user information.
- Client program that allows users to read and send emails and access the directory. Examples would include Outlook, Outlook on the web, and mobile devices such as Apple iPhone and Android devices.
- Client access interface that enables the client to retrieve email messages from a remote mail server. This could be a client/server protocol such as POP3 or IMAP4 or a web interface.
- Protocol that transports the mail reliably and efficiently, such as SMTP.
- Storage system for storing mail until a user retrieves them.
For on premise deployment of an email system, there are solutions from different vendors. The market leader is Microsoft Exchange server, providing email, scheduling, and related tools for custom collaboration and messaging service applications. As per a Gartner research when Gartner last tracked the on-premises email market back in 2012, Microsoft Exchange has more than 80% market share.
Microsoft Exchange Server Roles
Microsoft Exchange has evolved over a period of time to take advantage of increase in CPU horsepower. For instance, Microsoft Exchange Server 2010 had five roles which were consolidated into the following three roles in Microsoft Exchange Server 2013:
- Client Access server role: This is the server that clients (e.g. Outlook, Outlook Web App) connect to for mailbox access. The Client Access server authenticates and redirects or proxies those requests to the appropriate Mailbox server.
- Mailbox server role: This server hosts all the components and/or protocols that process, render and store the data. Mailbox servers can be added to a Database Availability Group, thereby forming a high available unit that can be deployed in one or more datacenters.
- Edge Transport server role: This server is optional and is typically deployed in your perimeter network, outside your internal Active Directory forest thereby minimizing the attack surface of your Microsoft Exchange environment. It can also it add additional layers of message protection and security against viruses and spam.
Microsoft further consolidated these into just two server roles in Microsoft Exchange 2016.
- Mailbox Server Role: The Mailbox server in Microsoft Exchange 2016 now includes all of the server components from the Microsoft Exchange 2013 Mailbox and Client Access server roles. In consists of:
– The transport services that are used to route mail.
– Mailbox databases that process, render, and store data.
– Client Access services that accept client connections for all protocols. These frontend services are responsible for routing or proxying connections to the corresponding backend services on a Mailbox server. Clients don’t connect directly to the backend services.
– Unified Messaging (UM) services that provide voice mail and other telephony features to mailboxes - Edge Transport Server Role: This role is optional and similar to one in Microsoft Exchange 2013.
Microsoft Exchange 2016 Architecture
The overall architecture of a Microsoft Exchange 2016 deployment is shown in the diagram below.
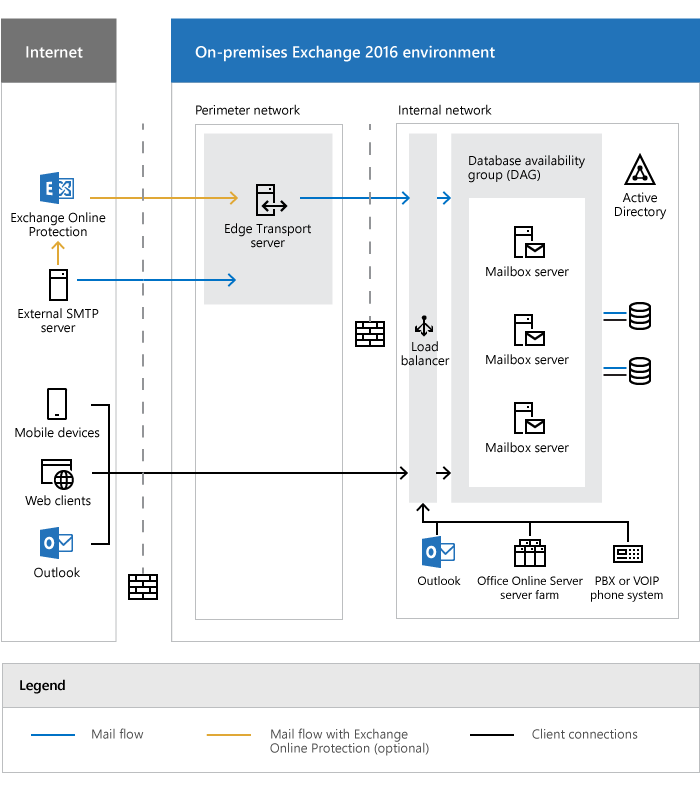
Microsoft Exchange 2016 Architecture
Deployment Criteria for Microsoft Exchange
The critical importance of email within an organization requires that any Microsoft Exchange deployment meet the following requirements:
- High Availability: To ensure that users are able to access Microsoft Exchange services without any disruption, it is essential that an enterprise deployment consist of multiple Mailbox servers. This is in turn requires a mechanism to monitor the health of these servers and direct the client traffic only to the Mailbox servers that are functioning properly.
- High Scalability and Performance: The deployment of multiple Microsoft Exchange servers by itself does not guarantee performance. To achieve this the client traffic needs to be distributed evenly across multiple Microsoft Exchange servers to ensure their optimal utilization while ensuring high quality end user experience.
- Secure Communication: Communication between the clients and the Microsoft Exchange servers needs to be secured using SSL with protocols such as HTTPS, POP3S etc. Additionally, you want to deploy SSL using the recommended best practices including disabling SSLv3, prioritize the use of Perfect Forward Secrecy ciphers, and transparently redirect client connections from HTTP to HTTPS among others.
- High Performance SSL: SSL encryption and decryption is a highly CPU intensive process and while it can be done on the Microsoft Exchange servers, it will reduce their performance and impact user experience. SSL encryption/decryption is best performed using specialized hardware optimized to perform this at a high rate.
- Defend Against DDoS Attacks: There are a variety of DDoS attacks such as Land Attack, Ping of Death etc. and to comprehensively defend your Microsoft Exchange infrastructure against such attacks without impacting the server performance you need to deploy additional security devices that are designed to detect and defend against such attacks.
- Defend Against Web Application Vulnerabilities: To protect Microsoft Exchange servers from web application attacks such as SQL Injection, Cross Site Scripting (XSS) etc. you need to deploy a Web Application Firewall that has specific knowledge of HTTP and web application vulnerabilities and thus can defend against these attacks.
- High Speed Authentication of Clients: While authentication of clients can be done by the Microsoft Exchange server, you can improve the performance of the servers and the overall end-user experience by offloading this task to another device that acts as an authentication proxy.
How A10 Networks Can Help
You can achieve all the key requirements listed above by deploying an application delivery controller with integrated DDoS and Web Application Firewall capabilities in front of the Microsoft Exchange servers. Thunder ADC can enhance your Microsoft Exchange server deployment by providing the following benefits:
- High availability for Microsoft Exchange Mailbox servers, ensuring that users can access Microsoft Exchange services anytime without disruption
- Higher scalability and connection to enhance end user experience
- Improved server performance due to server optimizations such as SSL offload.
- Highest levels of security with PFS/ECC ciphers, HSTS and HTTP-to-HTTPS redirection
- Protection against DDoS attacks using integrated DDoS protection capabilities
- Protection against web application attacks through web application firewall
- Secure authentication and access control using Application Access Management
A10 Networks’ AppCentric Templates enable the deployment of Microsoft Exchange 2016 with minimal effort.This will allow you to easily deploy the ADC with the recommended security best practices without having to manually configure the settings.
Thunder ADC Deployment with Microsoft Exchange
For more details on deploying Microsoft Exchange, see the following resources:
- Deployment guide for Microsoft Exchange 2016 with A10 Networks Thunder ADC
- Deployment guide for Microsoft Exchange 2013 with A10 Networks Thunder ADC
- Video of deploying Microsoft Exchange with AppCentric Templates
Learn more about A10’s application delivery products and load balancing solutions.
Seeing is believing.
Schedule a live demo today.