DDoS Threat Map Shows Global Distribution of Top Amplifier Weapons and Bots
A10 Networks has provided updated data on its threat map, highlighting, by country, the top amplification weapons and total bots/drones found in the latest global queries conducted by our threat research team. While this map illustrates where the weapons are hosted, attacks can be initiated and controlled by malicious actors across the globe using any of these weapons. To view a comprehensive set of data on DDoS weapons, download the full report.
DDoS attacks become more sophisticated and larger in volume every year. DDoS attacks today use multiple attack vectors from multiple countries to achieve high volume and obscure the origination of the attack. Data such as that found in the threat maps and in the A10 Defend Threat Control portal assists enterprise and service provider cyber threat teams in identifying and isolating suspicious activity in their networks for better protection against DDoS attacks.

In April 2025, a hyper-volumetric, multi-vector attack occurred at 6.5 Tbps and 4.8 billion packets per second. This is the largest reported DDoS attack to date. This attack used more than 30,000 unique IP addresses from 147 countries and multiple attack vectors, including SYN flood attacks, Mirai botnet, SSDP amplification, CLDAP and ESP reflection/amplification. The threat map provides details on where some of these weapons could be located.
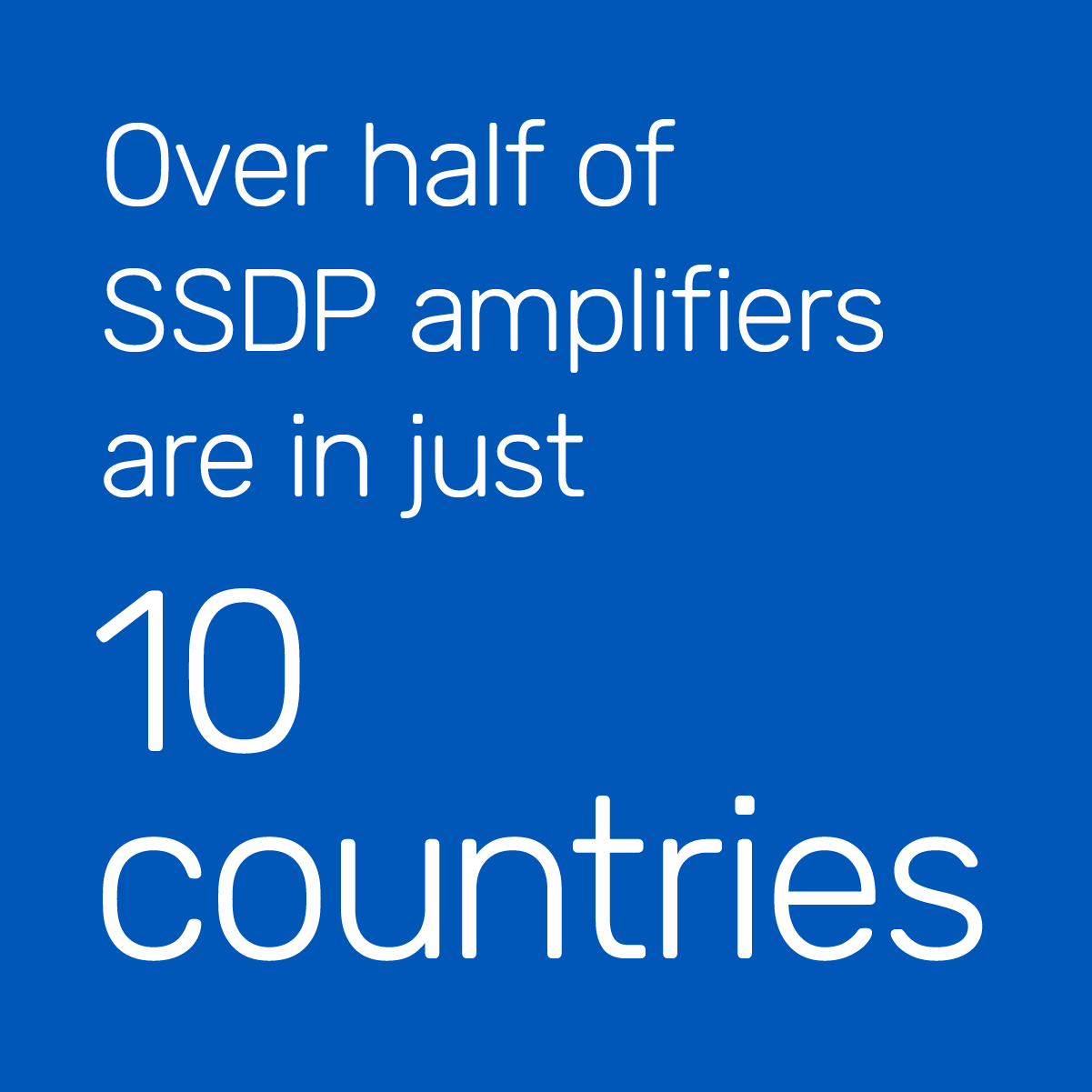
The Simple Service Discovery protocol (SSDP) is a commonly used attack vector for DDoS attacks. A10 research found millions of amplifier weapons globally, with heavy concentration in the U.S. and China. SSDP comprises about 22 percent of that total. Over half of the SSDP amplifiers are in just ten countries–Venezuela, China, Algeria, Croatia, South Korea, Vietnam, Taiwan, India, and Kazakhstan. The remaining amplifier weapons are distributed across two hundred countries.
SSDP allows devices on a local network to discover other devices automatically. This protocol is widely used in consumer devices including plug-and-play environments, home automation, media streaming and device configurations, smartphones, network cameras and others. There are millions of SSDP-based devices on a network, with millions exposed to the internet.
On the other hand, Connectionless Lightweight Directory Access Protocol (CLDAP) is a more obscure protocol, representing only 0.2 percent of all amplifiers globally. CLDAP is a network protocol primarily used for querying directories such as Microsoft Active Directory. Because CLDAP uses the User Datagram Protocol (UDP), it is vulnerable to abuse in reflection amplification attacks. Attackers can send small, spoofed requests to exposed CLDAP servers which will then generate responses to the victim of up to seventy times the size of the initial request. While CLDAP-based attacks have been reported since 2016, its use as an attack vector has been increasing.
The A10 threat map also shows distribution of the Constrained Application Protocol (CoAP). CoAP represents 4 percent of total global amplifiers, with CoAP-based weapons found in 155 countries. As shown on the map, over half of CoAP weapons are concentrated in just three countries–China, Russia, and the Philippines.
CoAP is a lightweight, web transfer protocol widely used with resource-constrained IoT and machine-to-machine devices such as sensors, controllers, smart home devices, wearables, and energy management. There are documented cases of reflected amplification DDoS attacks using CoAP, running over UDP. Research teams have measured the amplification factor as thirty-four times the original request.
The threat map is useful as a view of the relative geographic concentration of top amplification weapons and total bots for each country. The 2025 DDoS weapons report provides more detailed data.
